How to View AD Logs in Event Viewer or Netwrix Auditor
Native Solution vs. Netwrix Auditor for Active Directory
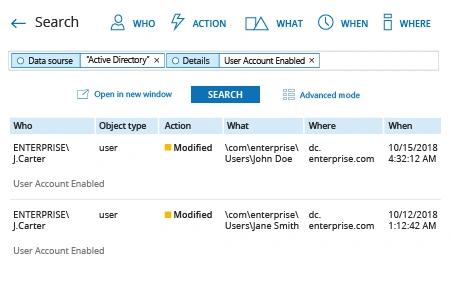
Netwrix Auditor for Active Directory
- Run Netwrix Auditor → Navigate to “Search” → Click on “Advanced mode” if not selected → Set up the following filters:
- Filter = “Data source”
Operator = “Equals”
Value = “Active Directory” - Filter = “Details”
Operator = “Contains”
Value = “User Account Enabled”
- Filter = “Data source”
- Click the “Search” button and review your report.
Native Solution
To register AD events you have to setup auditing first:
- Open the Group Policy Management console (gpmc.msc) on any domain controller in the target domain → Click Start → Go to Windows Administrative Tools (Windows Server 2016) or Administrative Tools → Choose Group Policy Management.
- Navigate to Domain Controllers. Right-click the effective domain controller’s policy and select Edit.
- In the Group Policy Management Editor, choose Computer Configuration → Go to Policies → Go to Windows Settings → Go to Security Settings → Go to Local Policies → Go to Audit Policy. Set the following audit policies:
- Audit account management: "Success"
- Audit directory service access: "Success"
- Audit logon events: "Success" and "Failure"
Alternatively, you can set Advanced audit policies: In the Group Policy Management Editor, expand Computer Configuration → Go to Policies → Go to Windows Settings → Go to Security Settings → Go to Advanced Audit Policy Configuration → Go to Audit Policies. Set the following audit policies:
- Account Management
- Audit Computer Account Management: "Success"
- Audit Distribution Group Management: "Success"
- Audit Security Group Management: "Success"
- Audit User Account Management: "Success"
- DS Access
- Audit Directory Service Access: "Success"
- Logon/Logoff
- Audit Logoff: "Success"
- Audit Logon: "Success"
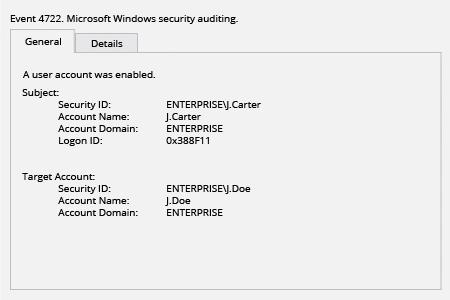
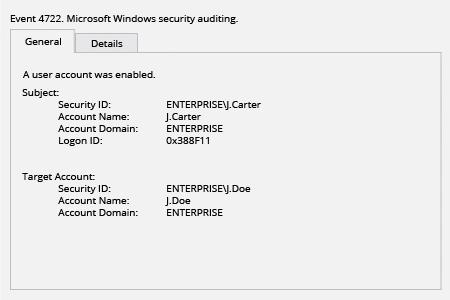
Each event type in log has its own Event ID. Below we're looking for “a user account was enabled” event.
- Right-click Start → Choose Event viewer.
- Click Windows logs → Choose the Security log.
- Click “Filter Current Log”.
- Specify event ID “4722” and click OK.
- Review the results.
Keep an Eye on Changes to Your Active Directory
Active Directory (AD) is critical for account management, including both computer and user accounts. In particular, the Active Directory service enables you to control access to data and applications on your file servers and other components of your network. Therefore, it is crucial to keep track of changes to your Active Directory and promptly spot any malicious or improper activity to ensure the security of your infrastructure and data. For example, you need to track changes to your GPOs.
Event Viewer is the native solution for reviewing security logs. It is free and included in the administrative tools package of every Microsoft Windows system. After you enable Active Directory auditing, Windows Server writes events to the Security log on the domain controller. The security event log registers the following information:
- Action taken
- The user who performed the action
- The success of the event and any errors that occurred
- The time the event occurred
You can export events from the Event Viewer. However, different types of events have different schema, which complicates parsing the events audit file. Also, Event Viewer require admins to learn the specific event ID numbers they want to search for or filter by, which further complicates monitoring of changes to AD objects. For instance, the article above shows how to filter logs for the “a user account was enabled” event.
Moreover, the native auditing solutions do not provide the complete visibility you need. The data is hard to read due to lack of formatting and the cryptic descriptions. On top of that, the event log search is slow: Even with default log size, you will have to spend significant time waiting for the search to finish, which will delay your threat response.
Unlike native solutions, Netwrix Auditor for Active Directory provides prebuilt and custom alerts and reports that translate event data from Active Directory logs into a clear, easy-to-read format. Instead of spending hours grubbing through log files with Event Viewer, Netwrix Auditor provides you with the data you need quickly and easily, helping to speed threat response and simplify preparation for compliance audits.
Share on
