See all products
Netwrix Access Analyzer: Data Protection Software
Stop juggling point tools. Unify data protection across your data sources, automate governance, and take control of AI adoption.
Read their Stories
Trusted by
































Why Netwrix?
Seal up breach points and gain control with data protection software
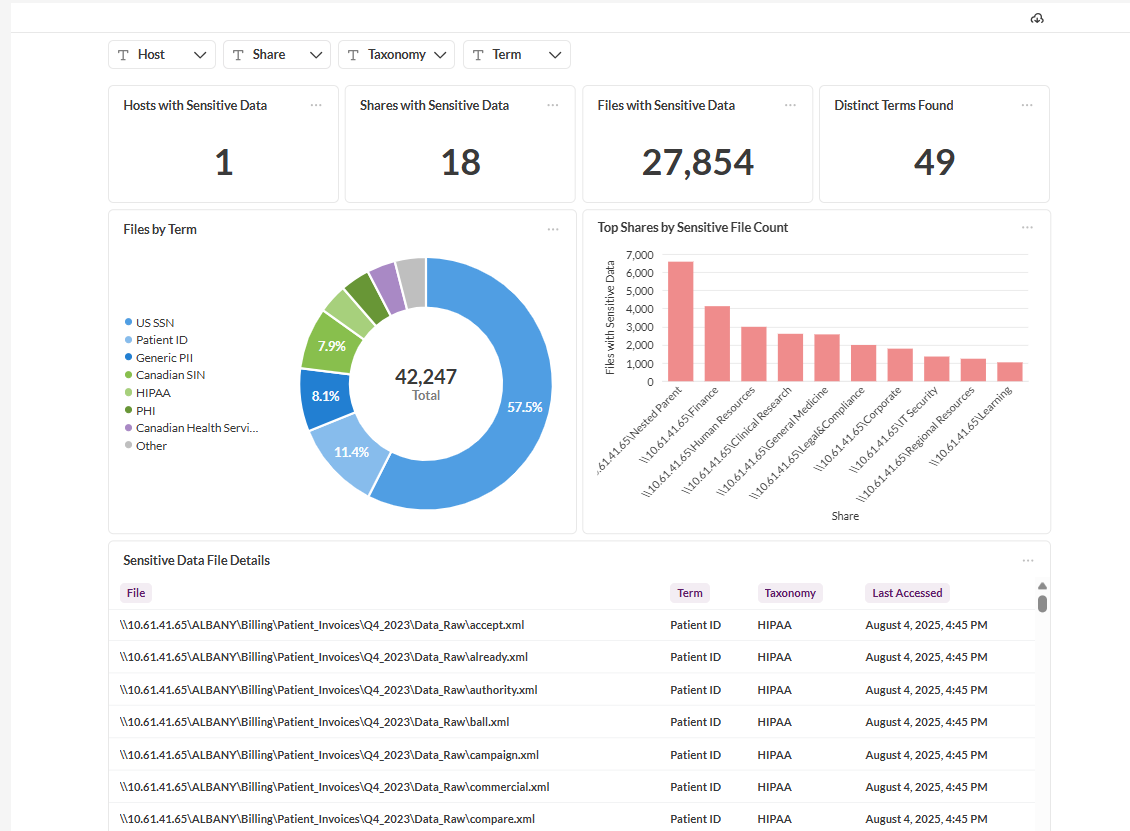
Find sensitive data everywhere
Automatically discover, classify, and apply MIP labels to sensitive data across on-premises and cloud data sources.
Automate access governance
Delegate access management to data owners and enforce least privilege principles with ease.
Simplify compliance reporting
Generate audit-compliant reports instantly and satisfy regulatory requirements fast.
Reduce the risk of a breach
Mitigate risks to sensitive data by identifying risks early, automating remediation, and keeping genAI from becoming an ungoverned path to sensitive data.
Capabilities
Discover, analyze, and protect across your entire infrastructure with enterprise-grade data protection solutions
Powerful data protection, wherever you work
See for yourself
Ready to get started?
Solutions
Go beyond single-threat protection. Secure every angle with Netwrix solutions.
Trusted by professionals
Don’t just take our word for it








