See which audit requirements
you can address to pass FFIEC audits
The provisions of the Gramm-Leach-Bliley Act (GLBA) that regulate the security of nonpublic personal information are presented in Title V – Privacy. These provisions stipulate that financial institutions doing business in the United States must establish appropriate information security controls to ensure the security and confidentiality of customer records and information, protect against unauthorized access to or use of such records or information which could result in substantial harm or inconvenience to any customer, and protect against any anticipated threats or hazards to the security or integrity of such records.
The Federal Financial Institutions Examination Council (FFIEC) designs and supervises audits for most federal agencies that oversee financial institutions. The FFIEC provides extensive guidelines for information security and risk management that help financial organizations achieve and prove compliance with GLBA safeguards and rules. Netwrix can help you pass GLBA audits by ensuring continuous compliance with the following FFIEC requirements:
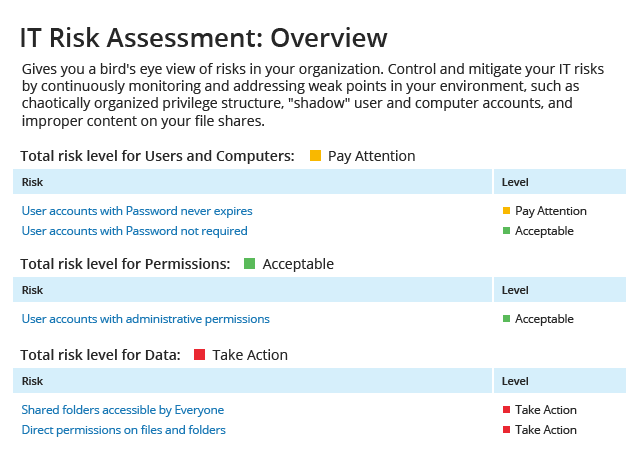
- II.A Risk Identification
- II.A.2 Vulnerabilities
- II.B Risk Measurement
- II.C Risk Mitigation
- II.C.5 Inventory and Classification of Assets
- II.C.7 User Security Controls
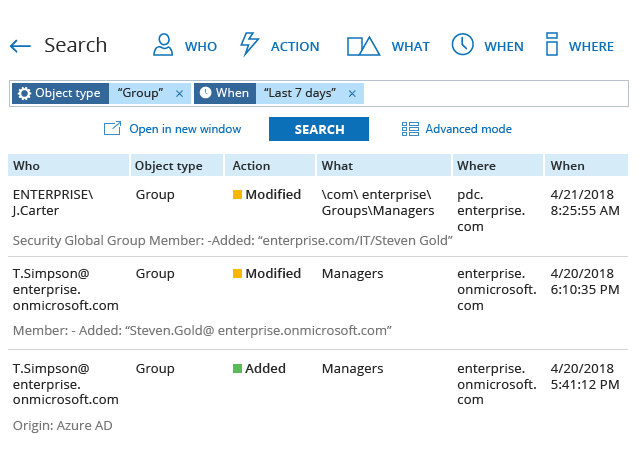
- II.C.7(c) Segregation of Duties
- II.C.10 Change Management Within the IT Environment
- II.C.10(a) Configuration Management
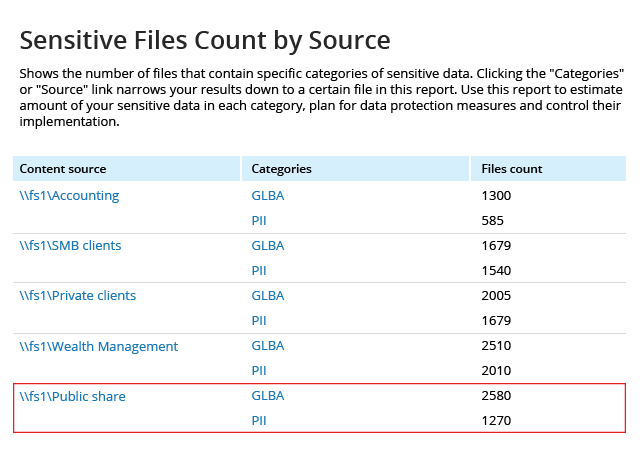
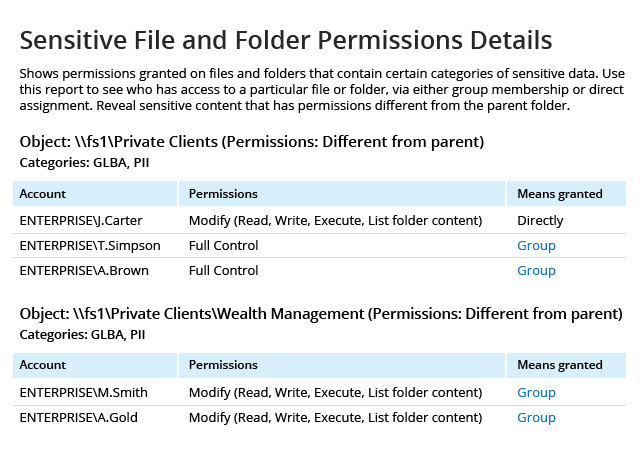
- II.C.13 Control of Information
- II.C.13(a) Storage
- II.C.15 Logical Security
- II.C.15(a) Operating System Access
- II.C.15(b) Application Access
- II.C.15(c) Remote Access
- II.C.18 Database Security
- II.C.22 Log Management
- II.D Risk Monitoring and Reporting
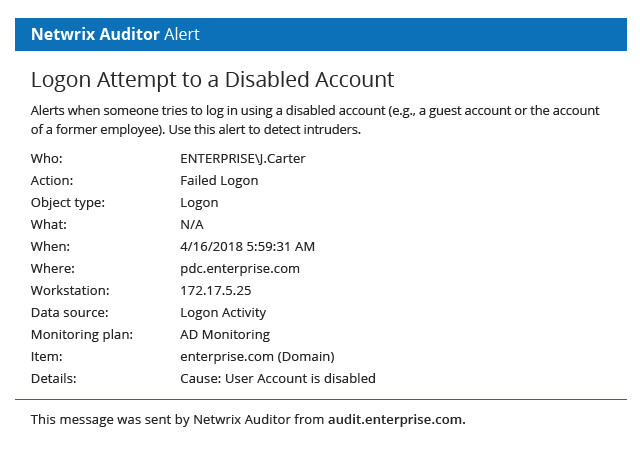
- III.A Threat Identification and Assessment
- III.B Threat Monitoring
- III.C Incident Identification and Assessment
- III.D Incident Response
Netwrix can help you pass
FFIEC compliance audits.
of your business and other
factors, Netwrix might also facilitate compliance with
provisions of the FFIEC IT Handbook not listed above.