Identity Threat
Detection & Response
Eliminate risks proactively
Prevent breaches by proactively uncovering and remediating risks and misconfigurations. Block risky changes and privilege escalation before damage occurs.
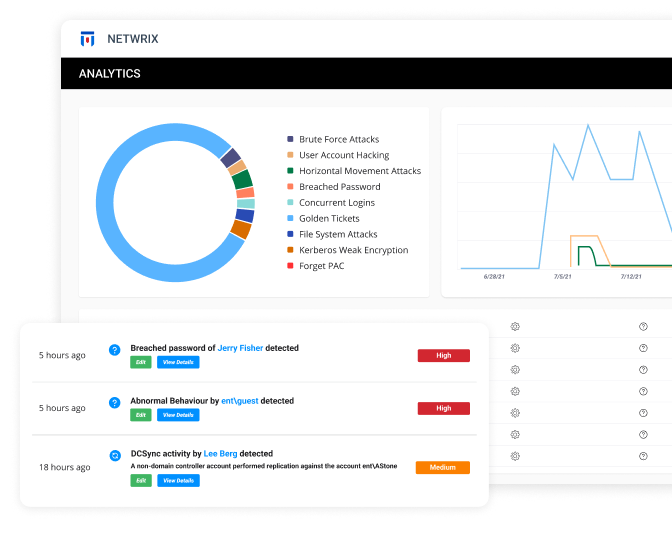
Stop attackers in their tracks
Detect in real time even the stealthiest threats lurking in AD and Entra ID. Instantly neutralize threats with automated response actions before they escalate.
Keep your business running
Ensure business continuity by quickly reversing unwanted changes and recovering deleted objects. Strengthen AD resilience with automated forest recovery, restoring operations fast.
Safeguard your Identity Infrastructure
Identify Weaknesses in Your Active Directory & Entra ID
Remediate Risks
Reduce your identity attack surface by eliminating dangerous misconfigurations, stale objects, and toxic permission conditions in bulk and at scale. Enhance security by enforcing least privilege principles and strong password policies across your enterprise identity ecosystem without burdening your team.
Prevent Threats
Detect Threats
Automate Threat Response
Investigate Identity-Based Attacks
Remediate Unwanted AD Changes
Slash your AD forest recovery time
PRODUCTS INCLUDED
Explore the Netwrix products that can help you secure your key identity systems — Active Directory & Entra ID
Explore related Netwrix solutions
Secure Privileged Access.
Why Netwrix
Patented Innovation
Complete Protection
Flexible and scalable