Meet New Netwrix
Auditor
Data Discovery
& Classification Edition:
Identify, Classify and Secure Sensitive Data on Your File Shares
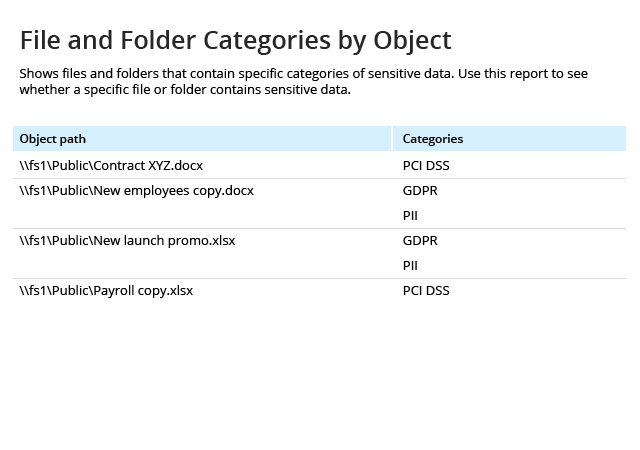
Where are your most sensitive files located?
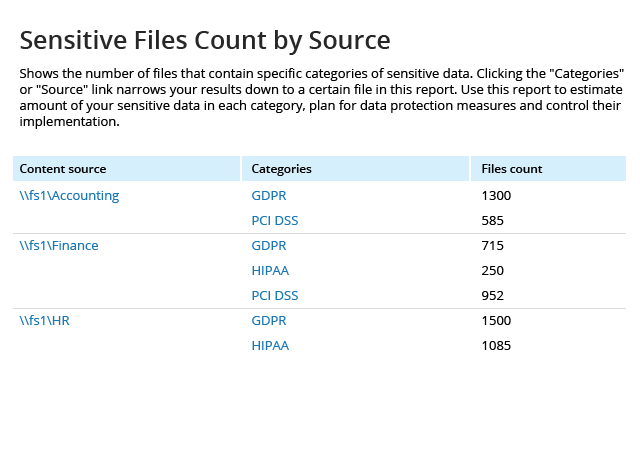
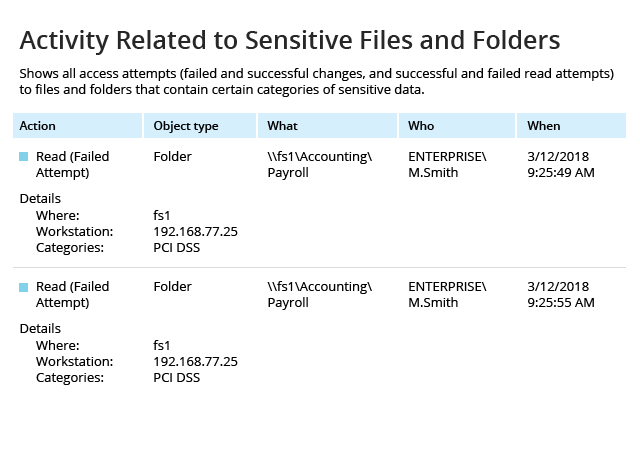
In order to protect PII, PHI, PCI or IP, you need to know where it is located. But modern environments are very dynamic, with business users copying and moving data all the time. Can you keep track of your most critical information? Do you know which folders contain sensitive data today? Tomorrow? Next week?
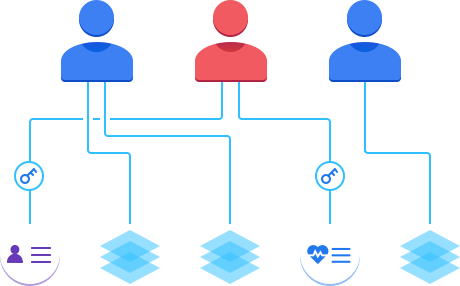
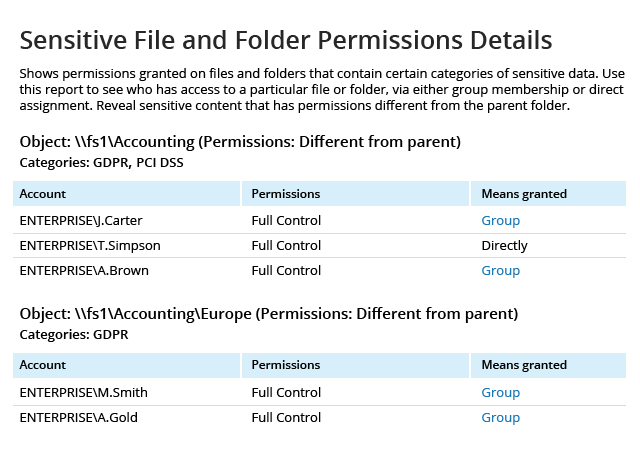
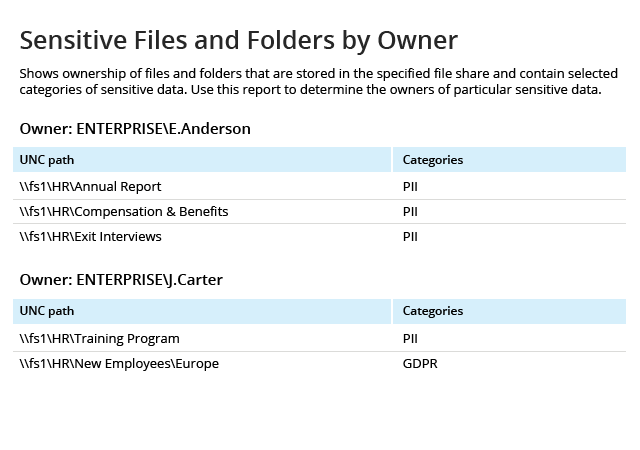
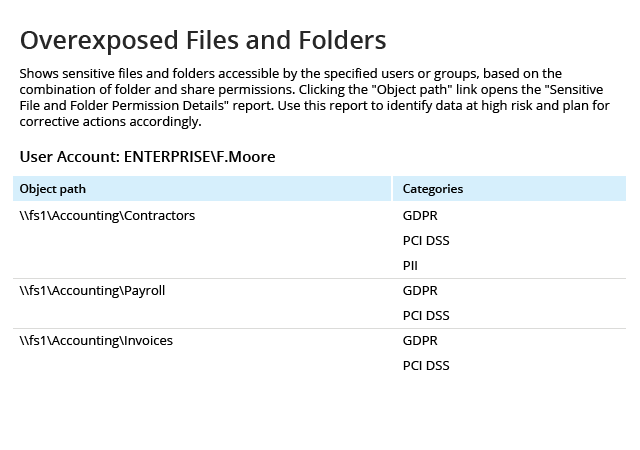
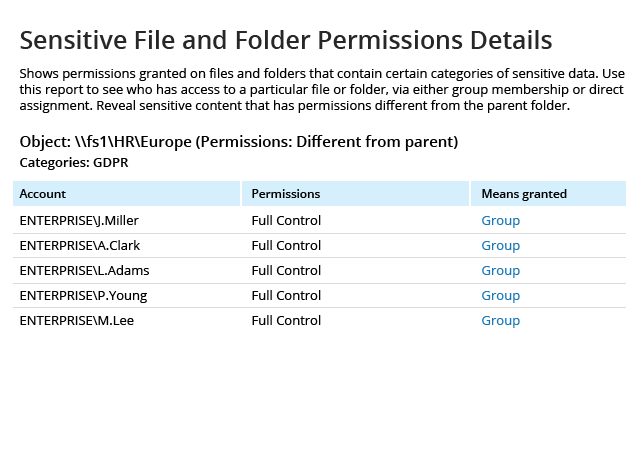
How can I keep my sensitive data secure?
Identifying where your sensitive content resides is just the first step. To minimize the risk of a data breach or non-compliance, you also need to be able to gather the relevant context and implement risk-appropriate controls around the data. Ask yourself the following questions:
How can I reduce the stress and costs
associated
with compliance audits?
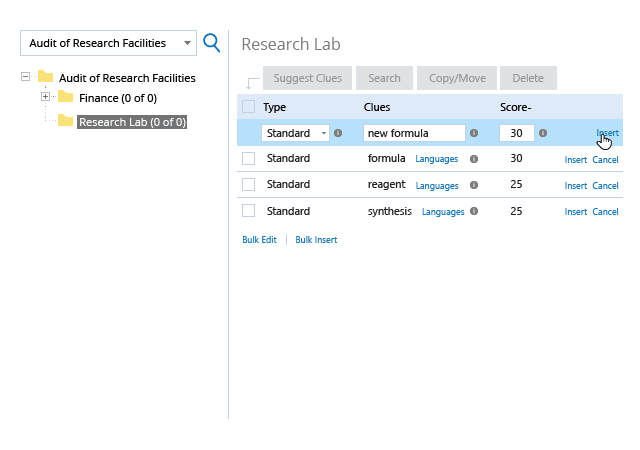
As the GDPR has shown, new regulations can cause serious waves in the IT industry. While you can’t predict which types of data you will need to secure next, you can have a flexible solution in place ready to discover sensitive data based on criteria that are relevant to you. Here’s how you can establish a solid foundation for compliance and streamline preparations for future IT audits.