Insider Threat Monitoring Software
Malicious insiders can cripple critical systems, copy and sell sensitive customer data,
and steal corporate secrets. With Netwrix Auditor, you can ensure that no trusted employee, partner
or contractor gets away with damaging your company. Using the complete visibility provided by
this solution, you can build a comprehensive insider threat management program that
facilitates detection, investigation and prevention of unauthorized
insider activity.
Launch In-Browser Demo
No need to deploy the product
Simplify insider threat detection
with continuous user activity monitoring and stay alert
to anomalous behavior in your environment
to anomalous behavior in your environment
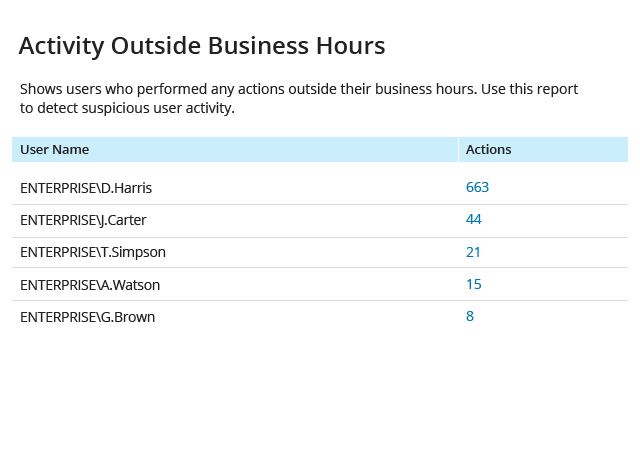
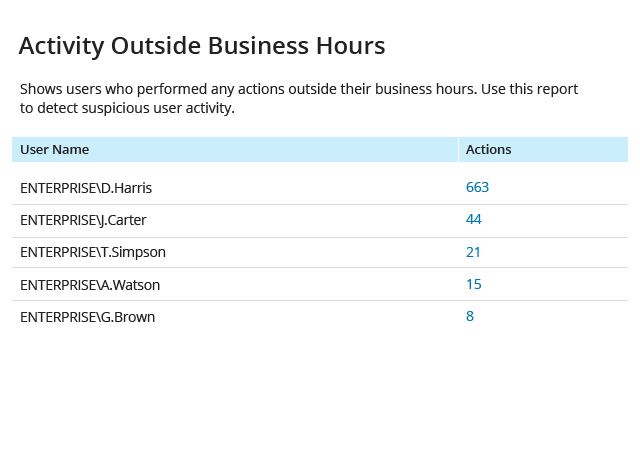
Identify who’s been active when everyone else is off
Review analytics on any user activity during non-business hours to detect an insider who’s crawling your network before you suffer a data breach.
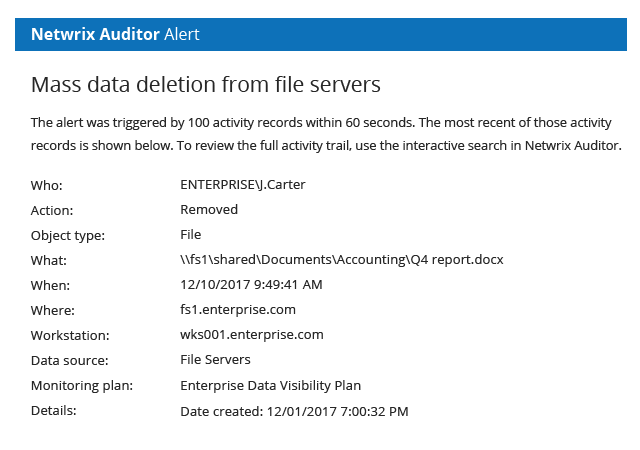
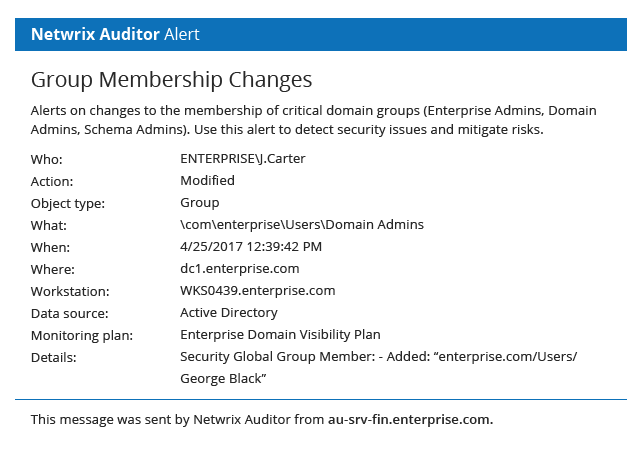
Get notified about high-risk insider threat patterns
Certain insider activity is a dead giveaway that insiders are tampering with your sensitive data. Set up alerts on events that you consider high-risk, and know about insider threats in time to respond effectively.
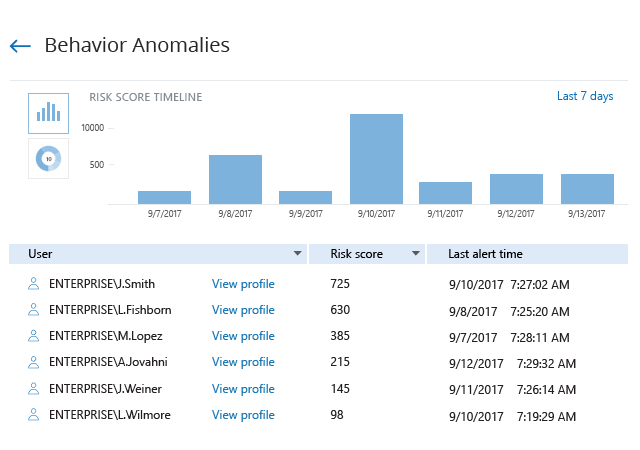
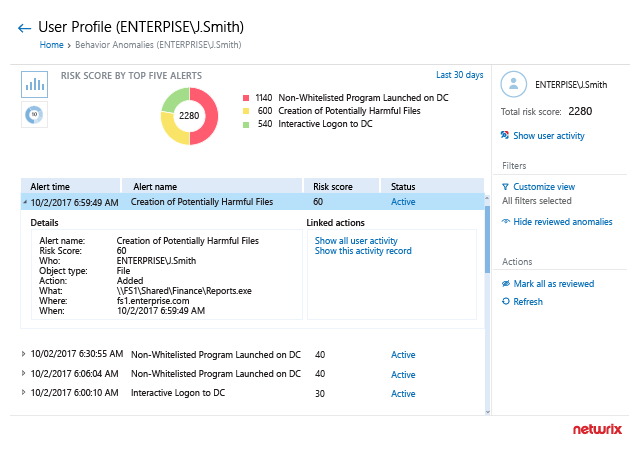
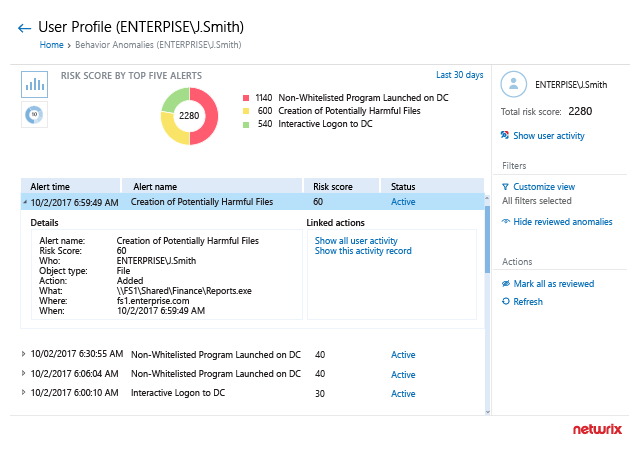
Enable threat detection with risk-based behavior anomaly discovery
Insiders tread carefully as they conduct reconnaissance and slowly home in on sensitive data. Make sure no malicious insider slips under your radar with a single view of all anomalous behavior in your environment.
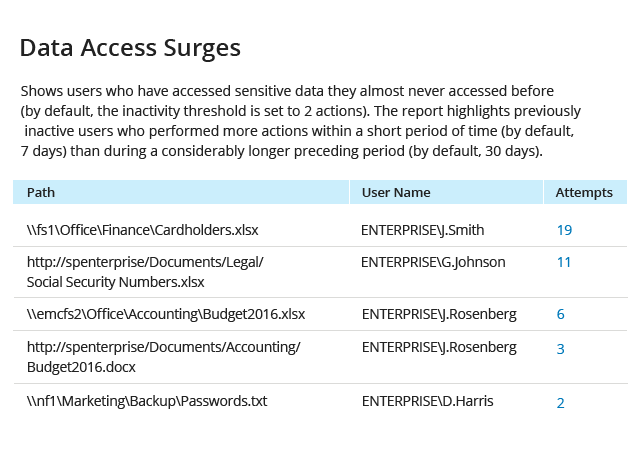
See when users are accessing sensitive data in unusual ways
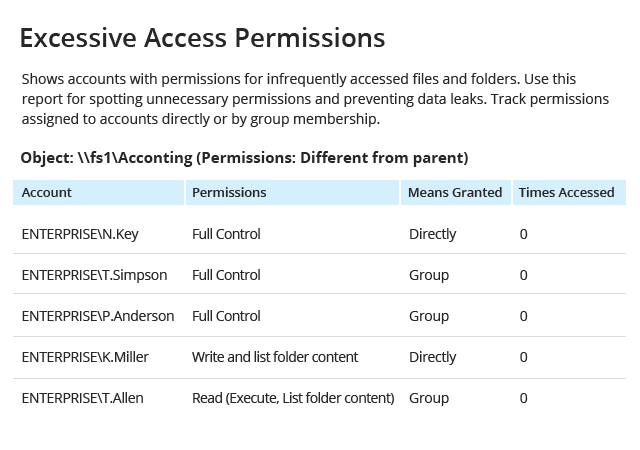
Boost your threat detection capabilities with threat intelligence reports. Spot malicious insiders with data theft on their minds by detecting users who are accessing sensitive information they almost never accessed before.
Identify who’s been active when everyone else is off
Review analytics on any user activity during non-business hours to detect an insider who’s crawling your network before you suffer a data breach.
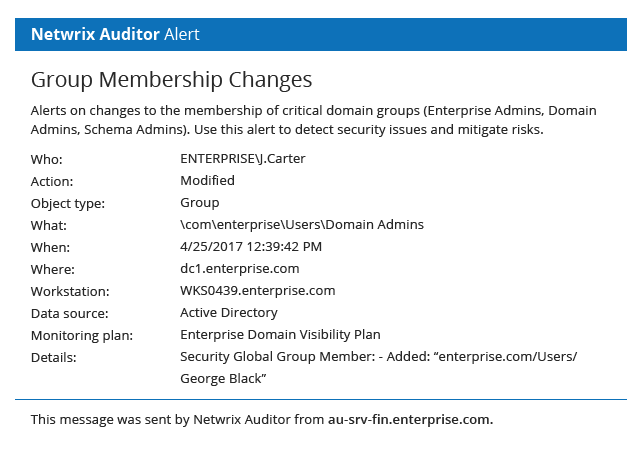
Get notified about high-risk insider threat patterns
Certain insider activity is a dead giveaway that insiders are tampering with your sensitive data. Set up alerts on events that you consider high-risk, and know about insider threats in time to respond effectively.
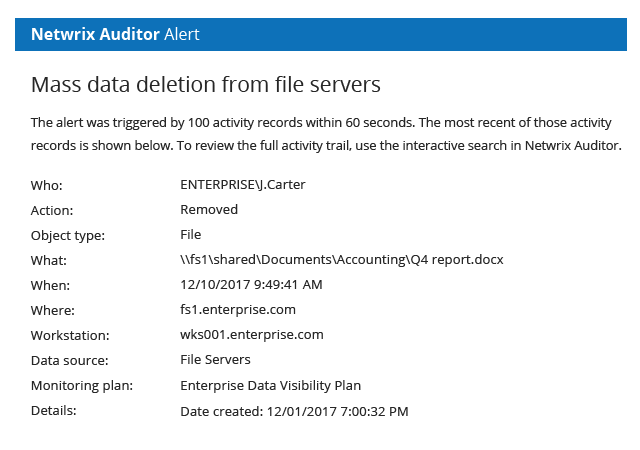
Get notified about high-risk insider threat patterns
Certain insider activity is a dead giveaway that insiders are tampering with your sensitive data. Set up alerts on events that you consider high-risk, and know about insider threats in time to respond effectively.
Enable threat detection with risk-based behavior anomaly discovery
Insiders tread carefully as they conduct reconnaissance and slowly home in on sensitive data. Make sure no malicious insider slips under your radar with a single view of all anomalous behavior in your environment.
See when users are accessing sensitive data in unusual ways
Boost your threat detection capabilities with threat intelligence reports. Spot malicious insiders with data theft on their minds by detecting users who are accessing sensitive information they almost never accessed before.
Identify who’s been active when everyone else is off
Review analytics on any user activity during non-business hours to detect an insider who’s crawling your network before you suffer a data breach.
Investigate incidents efficiently
with continuous insider threat monitoring to quickly find
the best response to each attack
the best response to each attack
Reconstruct insider attacks step by step
Review the profiles of high-risk users and analyze all anomalous activity triggered by these accounts to fully understand the scope of the attack and the damage they’ve done.
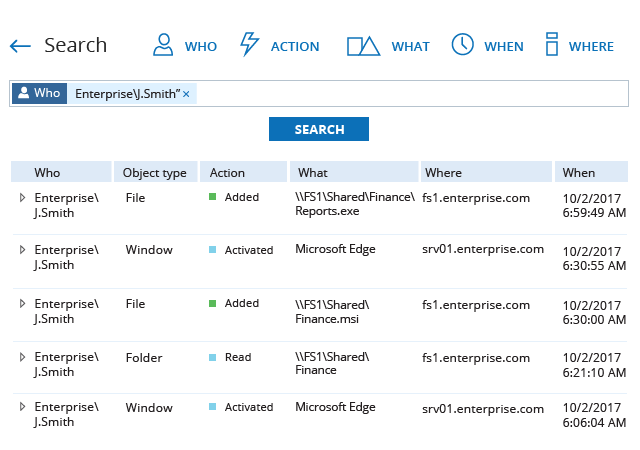
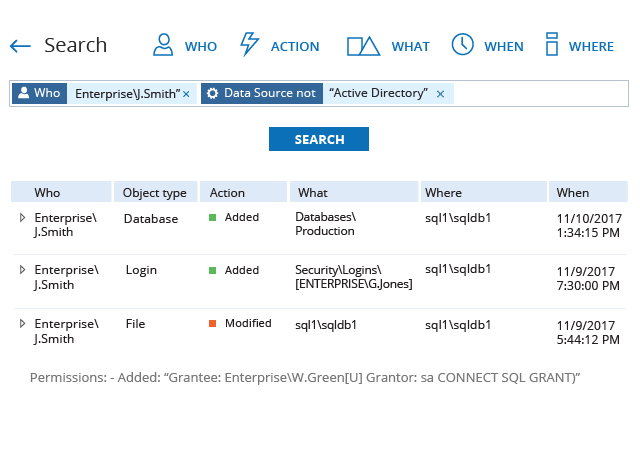
Initiate an in-depth, infrastructure-wide investigation
Review the complete user activity trail across all systems using the interactive search. The rich details provide the context of each user action, so you can understand how the attack was carried out and what actions allowed it to happen.
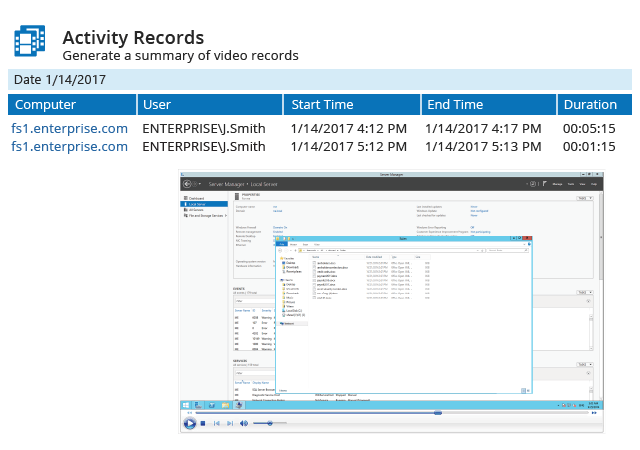
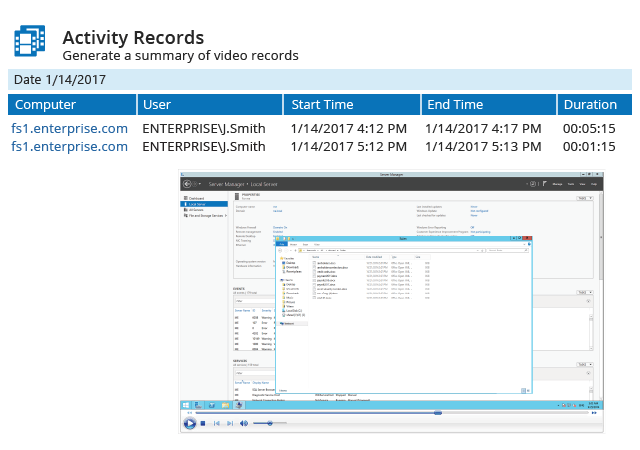
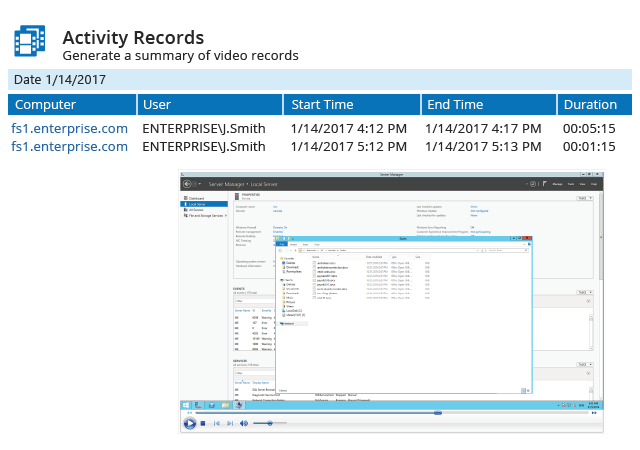
See how the attack unfolded with your own eyes
Record the screen activity of insiders in critical applications and on high-risk servers in your environment to get explicit evidence of the steps insiders took to achieve their goals.
See how the attack unfolded with your own eyes
Record the screen activity of insiders in critical applications and on high-risk servers in your environment to get explicit evidence of the steps insiders took to achieve their goals.
Reconstruct insider attacks step by step
Review the profiles of high-risk users and analyze all anomalous activity triggered by these accounts to fully understand the scope of the attack and the damage they’ve done.
Initiate an in-depth, infrastructure-wide investigation
Review the complete user activity trail across all systems using the interactive search. The rich details provide the context of each user action, so you can understand how the attack was carried out and what actions allowed it to happen.
See how the attack unfolded with your own eyes
Record the screen activity of insiders in critical applications and on high-risk servers in your environment to get explicit evidence of the steps insiders took to achieve their goals.
Reconstruct insider attacks step by step
Review the profiles of high-risk users and analyze all anomalous activity triggered by these accounts to fully understand the scope of the attack and the damage they’ve done.
Facilitate insider threat prevention
by proactively mitigating data security risks and continuously
monitoring
user access rights
monitoring
user access rights
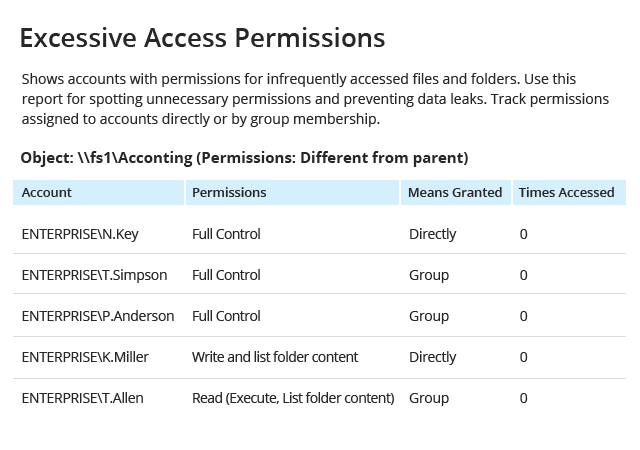
Identify overexposed sensitive data
Regularly perform privilege attestations to verify that your business users have access to sensitive data only if they need for their jobs. Quickly identify and revoke excessive permissions.
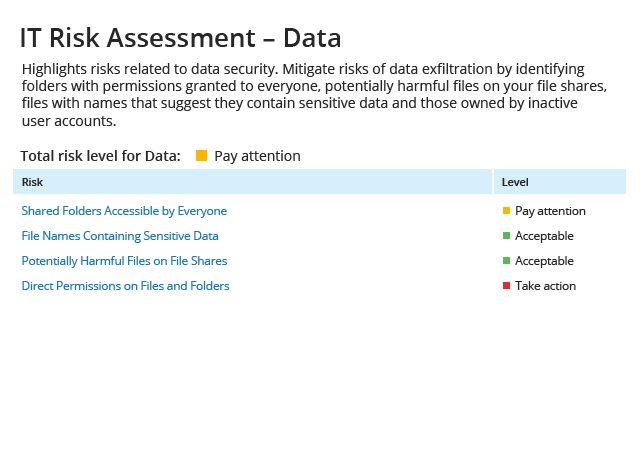
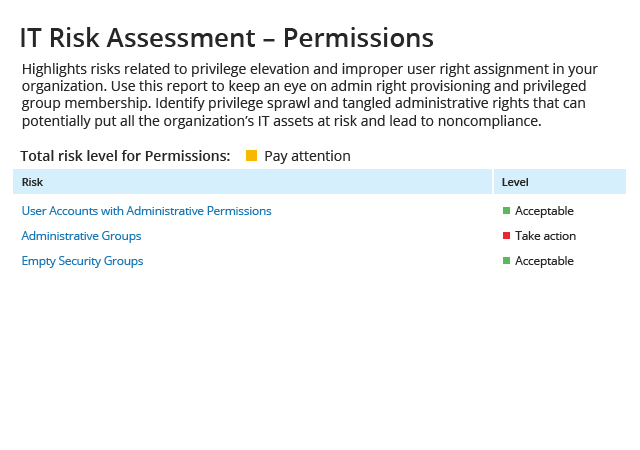
Remediate security weak spots before they are exploited
Make it as hard as possible for malicious insiders to steal your sensitive data by proactively remediating data security gaps in your environment. Netwrix Auditor calculates risk levels automatically, so you can harden the most impactful controls first.
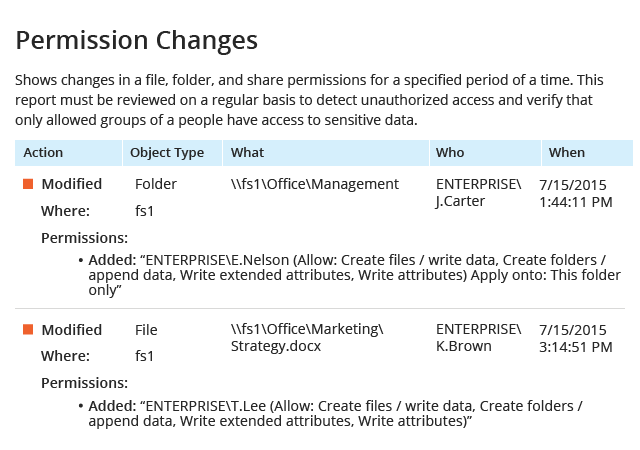
Prevent data exfiltration attempts by detecting unauthorized permission changes
Ensure that no access rights are assigned to users without a legitimate business need. Quickly identify inappropriate permission changes that give users access to sensitive information that they shouldn’t have, and remove them to prevent a data breach.
Identify overexposed sensitive data
Regularly perform privilege attestations to verify that your business users have access to sensitive data only if they need for their jobs. Quickly identify and revoke excessive permissions.
Remediate security weak spots before they are exploited
Make it as hard as possible for malicious insiders to steal your sensitive data by proactively remediating data security gaps in your environment. Netwrix Auditor calculates risk levels automatically, so you can harden the most impactful controls first.
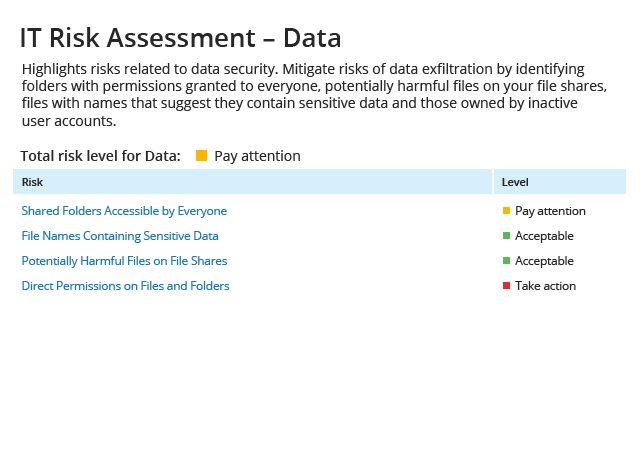
Remediate security weak spots before they are exploited
Make it as hard as possible for malicious insiders to steal your sensitive data by proactively remediating data security gaps in your environment. Netwrix Auditor calculates risk levels automatically, so you can harden the most impactful controls first.
Prevent data exfiltration attempts by detecting unauthorized permission changes
Ensure that no access rights are assigned to users without a legitimate business need. Quickly identify inappropriate permission changes that give users access to sensitive information that they shouldn’t have, and remove them to prevent a data breach.
Identify overexposed sensitive data
Regularly perform privilege attestations to verify that your business users have access to sensitive data only if they need for their jobs. Quickly identify and revoke excessive permissions.
Perform thorough privileged user monitoring
and pay close attention to the most powerful users
in your environment
in your environment
Stay on top of privileged user activity
Subscribe to reports on administrative activity in a particular system or across all of your environment to detect privilege abuse and keep your privileged users in check. Create alerts on critical behavior patterns that put data security at immediate risk.
Detect admins meddling with systems they are not responsible for
Use the flexible search to spot activity of administrators in systems they are not responsible for. If the search turns up any results, the listed users are abusing their privileges, putting sensitive data at risk. Create an alert so you can respond to these events even more quickly in the future.
Get concrete evidence of privilege abuse incidents
Protect your resources by monitoring privileged user activity. If a user works in applications or tools that do not produce any logs, be sure to replay and search through their screen activity.
Establish compliance with privilege account management best practices
Tangled administrative rights can leave you not even knowing who your privileged users are. Check your privilege-related risks and ensure that privilege rights assignment is transparent in your organization.
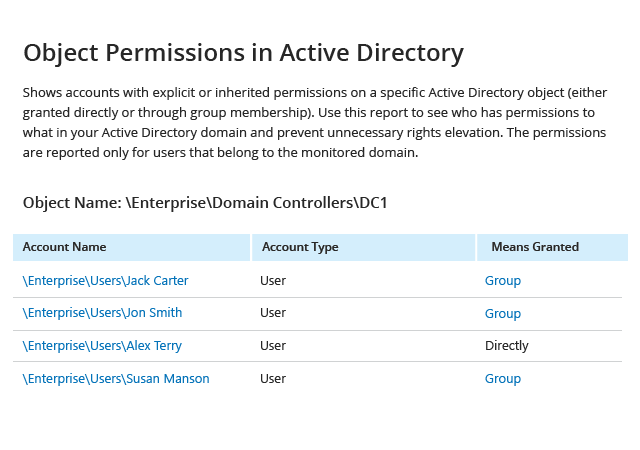
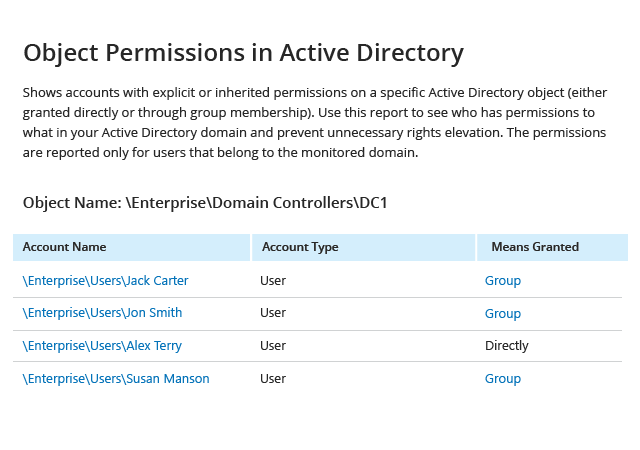
Perform privilege attestation for your administrators
Regularly review what permissions your users have in Active Directory to avoid privilege sprawl. If any permissions were granted directly to privileged users, start investigating immediately.
Perform privilege attestation for your administrators
Regularly review what permissions your users have in Active Directory to avoid privilege sprawl. If any permissions were granted directly to privileged users, start investigating immediately.
Stay on top of privileged user activity
Subscribe to reports on administrative activity in a particular system or across all of your environment to detect privilege abuse and keep your privileged users in check. Create alerts on critical behavior patterns that put data security at immediate risk.
Detect admins meddling with systems they are not responsible for
Use the flexible search to spot activity of administrators in systems they are not responsible for. If the search turns up any results, the listed users are abusing their privileges, putting sensitive data at risk. Create an alert so you can respond to these events even more quickly in the future.
Get concrete evidence of privilege abuse incidents
Protect your resources by monitoring privileged user activity. If a user works in applications or tools that do not produce any logs, be sure to replay and search through their screen activity.
Establish compliance with privilege account management best practices
Tangled administrative rights can leave you not even knowing who your privileged users are. Check your privilege-related risks and ensure that privilege rights assignment is transparent in your organization.
Perform privilege attestation for your administrators
Regularly review what permissions your users have in Active Directory to avoid privilege sprawl. If any permissions were granted directly to privileged users, start investigating immediately.
Stay on top of privileged user activity
Subscribe to reports on administrative activity in a particular system or across all of your environment to detect privilege abuse and keep your privileged users in check. Create alerts on critical behavior patterns that put data security at immediate risk.