SOX Compliance Software from Netwrix
See how Netwrix can help you pass compliance audits
Find out which COBIT principles you can address with Netwrix to achieve compliance with SOX
The Sarbanes-Oxley (SOX) Act was enacted in 2002 to enhance corporate responsibility, require financial disclosure, and combat corporate and accounting fraud. All public companies in the U.S., without exception, are subject to SOX compliance, including overseas operations of U.S. public companies and international companies listed on U.S. exchanges. SOX requires these companies to ensure internal control over financial reporting, while giving them the flexibility to select the “recognized control framework” of their choice. One of such frameworks is COBIT, which is focused on governance of enterprise information technology. However, it is aligned with another common framework, COSO, which provides more general guidance on internal control over financial reporting. These frameworks are more effective in tandem, since COBIT complements COSO in the area of IT controls required to be SOX compliant. The SOX compliance software solution from Netwrix supports the following COBIT principles:
- APO07 Manage Contract Staff: Requirement 06
- APO12 Manage Risk: Requirements 01, 02, 06
- APO13 Manage Security: Requirement 01
- APO14 Managed Data: Requirements 08, 09
- BAI08 Managed Knowledge: Requirement 02
- BAI10 Manage Configuration: Requirements 02, 04
- DSS01 Manage Operations: Requirement 03
- DSS02 Manage Service Requests and Incidents: Requirements 04, 05
- DSS05 Manage Security Services: Requirements 04, 06, 07
- DSS06 Managed Business Process Controls: Requirements 02, 03, 06
Depending on the configuration of your IT systems, your internal procedures, the nature of your business and other factors, Netwrix might also facilitate implementation of COBIT processes and practices not listed above.
See exactly how Netwrix solutions help you establish the controls required for SOX compliance
Netwrix solutions help with user behavior analysis and risk mitigation, and enables control over changes, configurations and access in hybrid IT environments. Netwrix provides security intelligence to identify security holes, detect anomalies in user behavior and investigate suspicious activities in time to prevent critical issues that can compromise your data security. Unlike many of the SOX compliance tools on the market, it delivers enterprise-wide visibility and provides the evidence required to prove you have internal controls that ensure the security of information systems and sensitive data — both on premises and in the cloud.
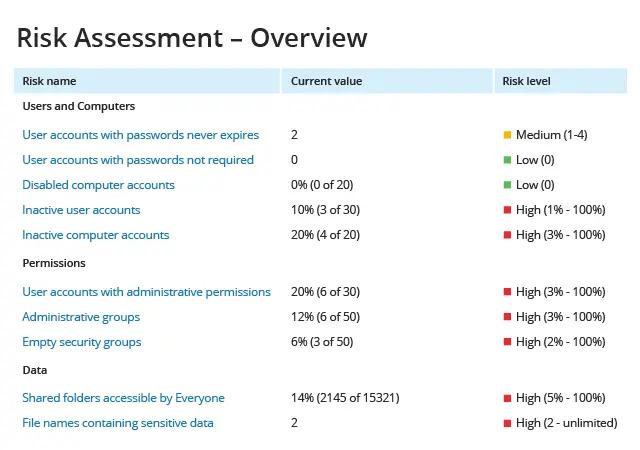
Demonstrate a proactive approach to identification and remediation of IT security gaps
Leverage IT Risk Assessment reports to strengthen your enterprise risk management practices. Identify security holes in three key areas of your IT environment — account management, security permissions and data governance — and use the security intelligence provided to reduce risks to data security.
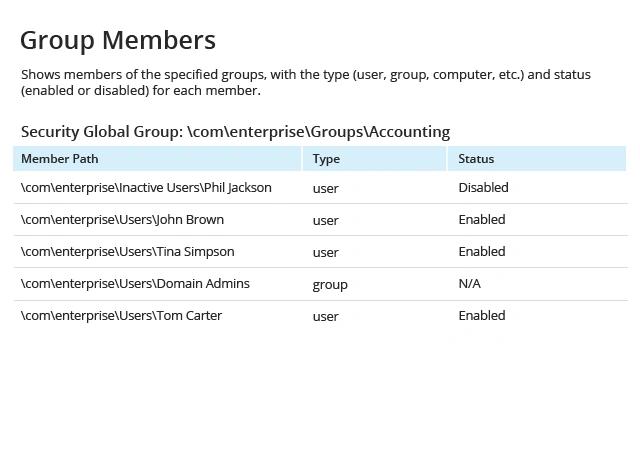
Ensure that only eligible users have access to financial applications and data
Regularly monitor the groups that have access to your important financial data and applications. Ensure that the design and membership of these security groups is in line with your compliance audit management program. Delete accounts with a “disabled” status in a timely manner, and avoid tangled group nesting.
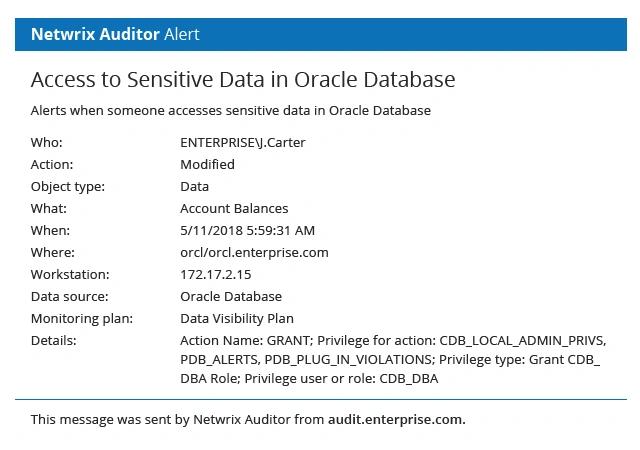
Stay on top of all access to your financial records
Get an automated notification any time someone accesses a database that contains financial records, so you can respond quickly to any suspicious access and prevent improper alteration of financial data. Alerts like this improve the efficiency of your incident detection processes.
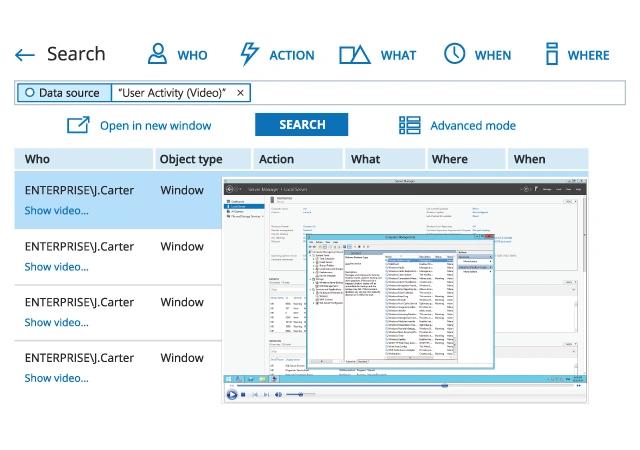
Prove to auditors that you have control over user activity in your financial applications
Implementation of video recording can help you keep business users who deal with accounting software under close surveillance and hold them accountable for their actions. It also gives you the evidence you need to prove the integrity of your financial reporting.
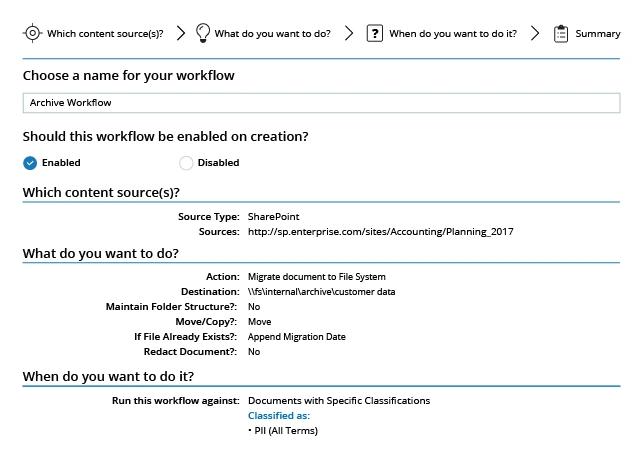
Comply with data archiving and retention requirements
Easily find all historical data in your organization and automatically move it to a dedicated archive location to enforce your retention policy and comply with regulatory requirements. You’ll also free up space on your file storage systems and cut down on clutter that impedes user productivity.
Share on
View related compliance concepts
Netwrix helps you comply with Korea’s National Network Security Framework (N2SF)
Netwrix helps you comply with APRA CPS 234
Netwrix helps you comply with the Philippines Data Privacy Act (DPA)
Netwrix helps you comply with India’s Digital Personal Data Protection (DPDP) Act
Netwrix helps you comply with Indonesia’s Personal Data Protection (PDP) Law
