Como obter o inventário de servidores em sua rede
Netwrix Auditor para Windows Server
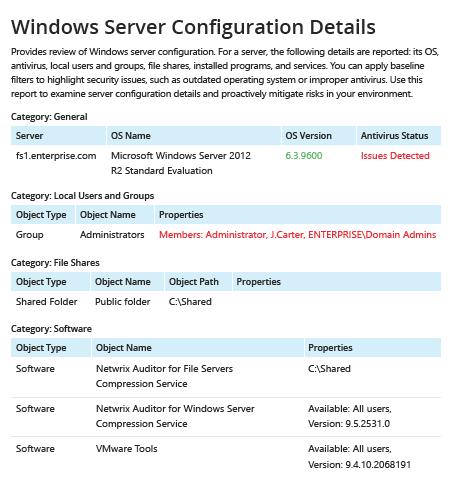
- Execute o Netwrix Auditor → Acesse "Relatórios" → Expanda a seção "Windows Server" → Vá para "Windows Server – State-in-Time" → Selecione "Detalhes de Configuração do Windows Server" → Clique em "Visualizar".
- Para salvar o relatório, clique no botão "Exportar" → Escolha um formato no menu suspenso → Clique em "Salvar".
Saiba mais sobre Netwrix Auditor for Windows Server
Auditoria Nativa
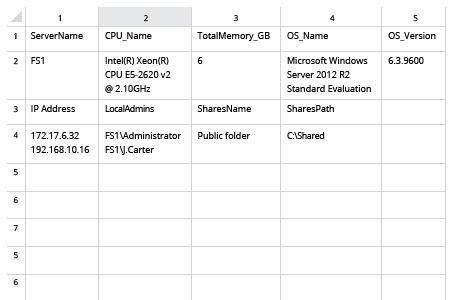
- Crie um arquivo contendo a lista de computadores → Abra o Powershell ISE → Execute o seguinte script, ajustando o caminho para a exportação:
#Start PSRemoting.
Invoke-Command -ComputerName (Get-Content C:\data\computers.txt) -scriptblock {
#Run the commands concurrently for each server in the list
$CPUInfo = Get-WmiObject Win32_Processor #Get CPU Information
$OSInfo = Get-WmiObject Win32_OperatingSystem #Get OS Information
#Get Memory Information. The data will be shown in a table as GB, rounded to the nearest second decimal.
$PhysicalMemory = Get-WmiObject CIM_PhysicalMemory | Measure-Object -Property capacity -Sum | % {[math]::round(($_.sum / 1GB),2)}
#Get Network Configuration
$Network = Get-WmiObject Win32_NetworkAdapterConfiguration -Filter 'ipenabled = "true"'
#Get local admins.
$localadmins = Get-CimInstance -ClassName win32_group -Filter "name = 'administrators'" | Get-CimAssociatedInstance -Association win32_groupuser
#Get list of shares
$Shares = Get-WmiObject Win32_share | Where {$_.name -NotLike "*$"}
$infoObject = New-Object PSObject
#Add data to the infoObjects.
Add-Member -inputObject $infoObject -memberType NoteProperty -name "ServerName" -value $CPUInfo.SystemName
Add-Member -inputObject $infoObject -memberType NoteProperty -name "CPU_Name" -value $CPUInfo.Name
Add-Member -inputObject $infoObject -memberType NoteProperty -name "TotalMemory_GB" -value $PhysicalMemory
Add-Member -inputObject $infoObject -memberType NoteProperty -name "OS_Name" -value $OSInfo.Caption
Add-Member -inputObject $infoObject -memberType NoteProperty -name "OS_Version" -value $OSInfo.Version
Add-Member -inputObject $infoObject -memberType NoteProperty -name "IP Address" -value $Network.IPAddress
Add-Member -inputObject $infoObject -memberType NoteProperty -name "LocalAdmins" -value $localadmins.Caption
Add-Member -inputObject $infoObject -memberType NoteProperty -name "SharesName" -value $Shares.Name
Add-Member -inputObject $infoObject -memberType NoteProperty -name "SharesPath" -value $Shares.Path
$infoObject
} | Select-Object * -ExcludeProperty PSComputerName, RunspaceId, PSShowComputerName | Export-Csv -path C:\data\Server_Inventory_$((Get-Date).ToString('MM-dd-yyyy')).csv -NoTypeInformation
- Abra o arquivo produzido pelo script no MS Excel.
Coletar Inventário de Servidor para Detectar Desvios de uma Linha de Base Conhecida
Para garantir que você tenha um entendimento preciso dos seus ativos críticos, é necessário um inventário completo e atualizado de hardware e um inventário de software detalhado que inclua quais servidores Windows você possui em seu domínio, qual versão do sistema operacional eles executam (como Windows Server 2012 ou Windows Server 2008) e se estão bem protegidos contra ataques externos. Um script PowerShell para coletar inventário de servidores pode ajudá-lo a obter uma lista de servidores. No entanto, reunir todos os detalhes importantes e produzir um relatório útil requer tempo, esforço e um sólido conhecimento de PowerShell.
Netwrix Auditor for Windows Server fornece todos os detalhes de que você precisa sobre todos os servidores da sua organização em um relatório abrangente e fácil de ler, que você pode exportar facilmente para um arquivo CSV e usar no Excel, ou para um arquivo PFD. O relatório é rico em informações, como o nome e a versão do sistema operacional instalado em cada servidor e o status do antivírus. Basta aplicar filtros ao relatório para detectar quaisquer desvios da sua linha de base adequada, para que você possa tomar medidas imediatas para reforçar a segurança dos seus computadores e dados.
Compartilhar em
