How to Get Local Users with or without PowerShell
Native Auditing
- Create a file containing the computer list.
- Open the Powershell ISE → Run the following script, adjusting the file name and path for the export:
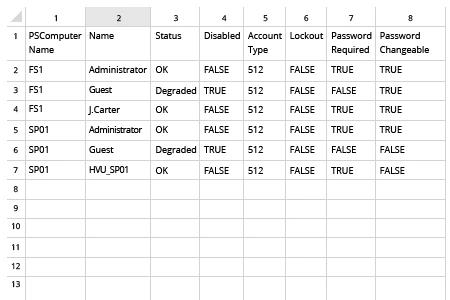
$computers = Get-Content -Path C:\data\computers.txt Get-WmiObject -ComputerName $computers -Class Win32_UserAccount -Filter "LocalAccount='True'" |
Select PSComputername, Name, Status, Disabled, AccountType, Lockout, PasswordRequired, PasswordChangeable, SID | Export-csv C:\data\local_users.csv -NoTypeInformation
- Open the file produced by the script in MS Excel.
Netwrix Auditor for Windows Server
- Run Netwrix Auditor → Navigate to "Reports" → Expand the "Windows Server" section → Go to "Windows Server – State-in-Time" → Select "Local Users and Groups" → Click "View".
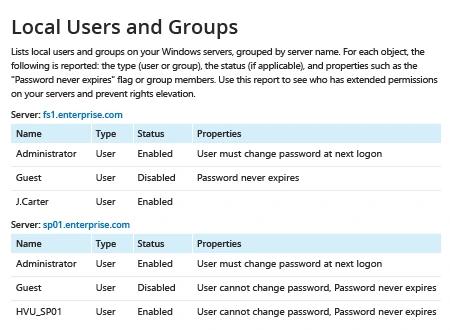
- To save the report, click the "Export" button → Choose a format from the dropdown menu → Click "Save".
Share on
