How to Enable Video Recording of Changes in Your Windows Server
Native Solution vs. Netwrix Auditor for Windows Server
Netwrix Auditor for Windows Server
With Netwrix Auditor, you need to enable video recording just once. To enable video recording for a particular workstation:
- Run Netwrix Auditor → Navigate to the "Monitoring Plans" tile → Select "Add Plan" → Fill out details and add a new plan.
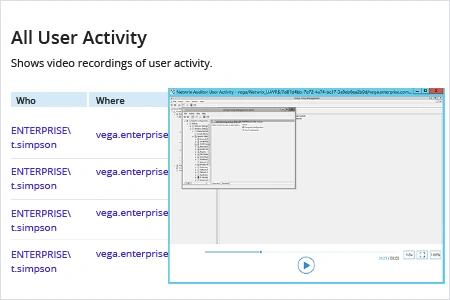
- To view a video record, go back to the main Netwrix Auditor page and navigate to "Reports" → Expand the "Windows Server" section → Go to "User Activity" → Select "All User Activity" → Click "View" → Specify the "From:" and "To:" values → Click "View Report" → Click on the desired time to play the video.
Native Auditing
With native auditing, you need to run a standalone tool each time you want to record user activity on a specific workstation.
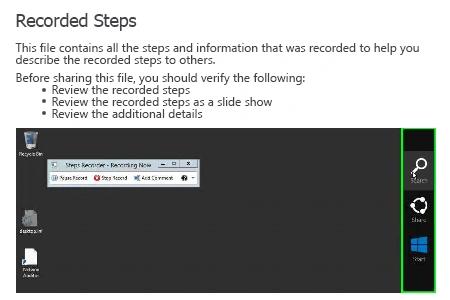
- Run PSR.exe (Steps Recorder) → Click "Start Record".
- Perform the necessary changes → click "Stop Record".
- Click "Save As" → Select the path where you want to save the recorded data → Click "Save".
- To view the recorded steps, open the produced mht file in Internet Explorer → Review the screenshots with the recorded steps.
Learn more about Netwrix Auditor for Windows Server
Spot and Investigate Unauthorized Changes with Video Recording of User Activity
Privileged users have the ability to make changes that can lead to unavailability of critical systems and security breaches. Therefore, it’s essential to keep privileged users accountable by monitoring their activity in critical systems and applications. One of the most effective options is video recording which enables IT pros to watch privileged users’ activity. Video recordings can provide valuable insight into the activity of privileged users, and knowing that activity is being recorded can deter users from making unauthorized.
Netwrix Auditor for Windows Server delivers complete visibility into Windows Server changes by providing key details about each change, including the before and after values. It also provides video recording of user screen activity to deliver deep visibility into the activity of privileged users across critical systems— even systems that do not produce any logs. IT admins can search and replay the recording to drill down into details and ensure no activity goes unnoticed. This feature is invaluable for investigating the root cause of a security issue.
Share on
