Back
Netwrix Auditor: The Microsoft Office 365 Monitoring Software
Get complete visibility into what’s going on in SharePoint Online, Exchange Online, and Teams environments with Office 365 monitoring software.
Read their Stories
Trusted by































Why Netwrix?
Comprehensive Microsoft 365 audit software that’s simple yet effective
Unlock unified monitoring
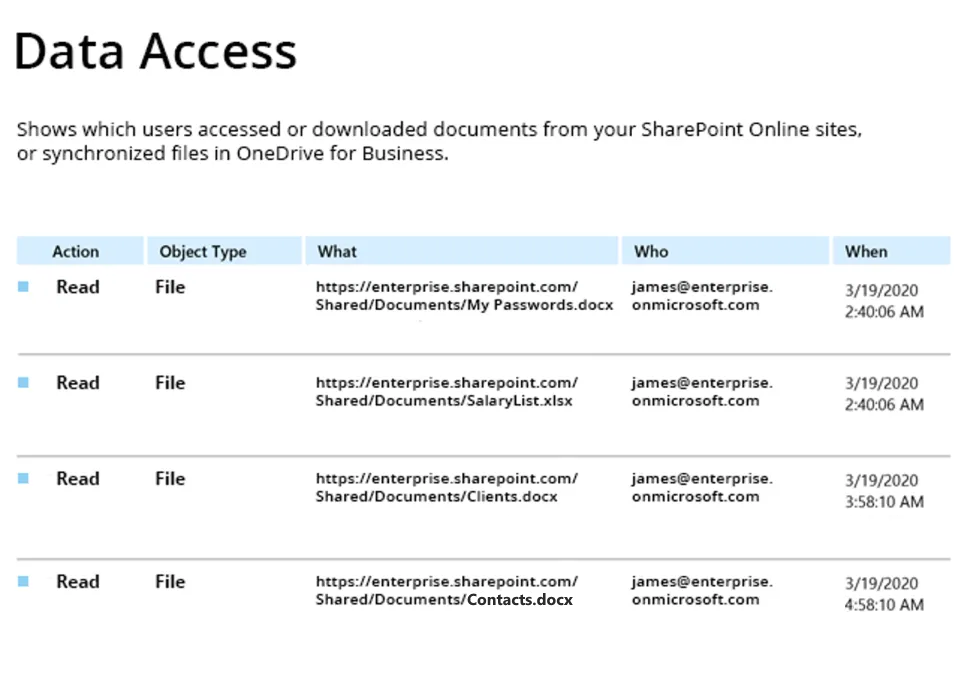
Monitor SharePoint, Exchange, and OneDrive from a single dashboard, eliminating the need to juggle multiple admin centers and log sources.
Pass audits with less effort
Streamline compliance using out-of-the-box reports aligned with GDPR, PCI DSS, FISMA/NIST, HIPAA, and many other regulations.
Boost IT team productivity
Quickly uncover, investigate, and remediate critical changes with Office 365 monitoring software — no digging through cryptic native logs.
Automate threat detection
Spot suspicious activity patterns like after-hours access and bulk downloads before your sensitive data walks right out the door.
Capabilities
Run Microsoft 365 audits effortlessly and prove compliance fast — without drawing in native audit logs
See for yourself
Ready to get started?
Solutions
Go beyond single-threat protection. Secure every angle with Netwrix solutions.
Trusted by professionals
Don’t just take our word for it







