See all products
Netwrix Change Tracker: Security Configuration Management Software
File integrity and security configuration management software that hardens systems, benchmarks settings, and proves compliance.
Read their Stories
Trusted by































Why Netwrix?
Root out unauthorized changes and harden your infrastructure
Harden critical systems
Strengthen security configurations across your entire infrastructure with our security configuration manager tool.
Instant change detection
Monitor unauthorized changes in real-time with advanced file integrity scanning and instant alerts for rapid response.
Real-time change validation
ITSM integrations provide closed-loop intelligent change control and reduce the noise from changes that were planned.
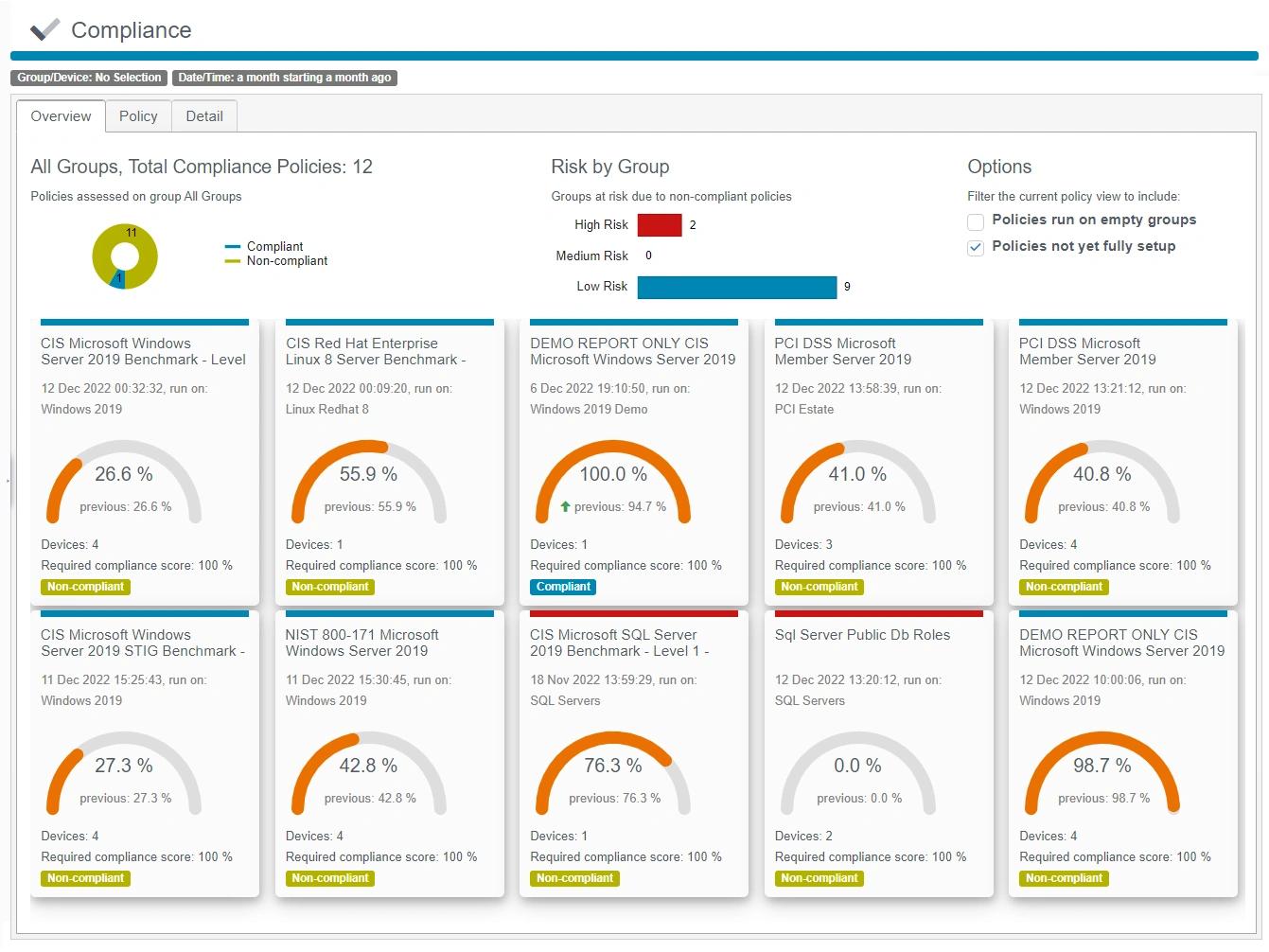
Meet compliance requirements
Pass regulatory audits easily with complete security configuration management tools and automated reporting.
Capabilities
Monitor, detect, and respond to changes across your entire IT infrastructure with complete security configuration management tools
See for yourself
Ready to get started?
Solutions
Go beyond single-threat protection. Secure every angle with Netwrix solutions.
Trusted by professionals
Don’t just take our word for it








