How to Detect File Changes in a Shared Folder
Netwrix Auditor for File Servers
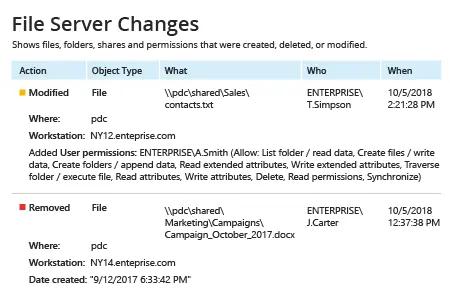
- Run Netwrix Auditor → Navigate to “Reports” → Expand the “File Servers” section→ Go to “File Servers Activity” → Select "File Server Changes" → Click "View".
- To save the report, click the "Export" button → Choose a format from the dropdown menu → Click “Save”.
Learn more about Netwrix Auditor for File Servers
Native Auditing
- Navigate to the file share → Right-click it and select "Properties" → Go to the "Security" tab → Click the "Advanced" button → Go to the "Auditing" tab → Click the "Add" button → Select Principal: "Everyone"; Select Type: "All"; Select Applies to: "This folder, subfolders and files" → Select the following "Advanced Permissions": Сreate files/write data, сreate folders/append data, Write attributes, Write extended attributes.
- Run gpedit.msc → Configure Default Domain Policy → Computer Configuration → Policies → Windows Settings → Security Settings → Local Policies → Audit Policy → Audit object access → Define "Success and Failures".
- In the "Advanced Audit Policy Configuration", adjust Audit File System → Define "Success and Failures" and “Audit Handle Manipulation” → Define "Success and Failures".
- Go to Event Log → Set "Maximum security log size" to 1 GB and "Retention method for Security log" to "Overwrite events as needed".
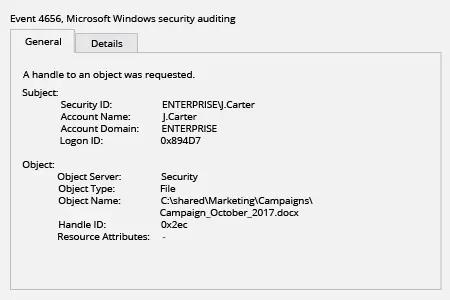
- Open "Event viewer" → Search the Security Windows Logs for the event ID 4656 with the "File System" or "Removable Storage" task category and with the "Accesses: WriteData" string. "Subject Security ID" will show you who changed the file.
Automate Auditing of File Changes to Quickly Spot Malicious Modifications
File changes in a shared folder, such as the deletion or relocation of files, can lead to information loss or even leaks of sensitive data — which in turn can result in reduced revenue, legal penalties and damage to the organization’s reputation. Therefore, IT pros need to monitor file changes in shared folders on Windows-based file servers. Comprehensive continuous monitoring enables IT staff to spot every suspicious file change in a timely manner and get the actionable details required for security investigations.
Netwrix Auditor for Windows File Servers enables you to monitor file changes across your Windows-based file servers. The application performs file change monitoring and delivers reports with all the critical who, what, where and when details. Google-like, interactive data search gives you the flexibility to find detailed information on particular users, such as all the files they have touched. This feature is particularly useful when it comes to investigating suspicious file activity, such as all file changes in the Accounting folder made by a particular HR employee.
Share on
