How to Track Who Deleted a File from Your Windows File Servers
Native Auditing vs. Netwrix Auditor for Windows File Servers
Netwrix Auditor for Windows File Servers
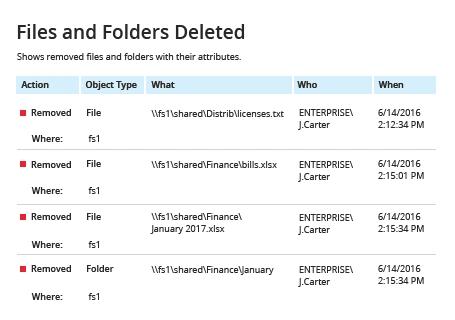
- Run Netwrix Auditor. Navigate to “Reports” → Click “File Servers” → Select “File Servers Activity” → Click “Files and Folders Deleted” → Click “View”.
- Type the server name in the “Where” field. You also can specify the path to a particular folder, using % as a wildcard character.
- Review the report:
Setting up file system auditing
- Navigate to the file share, right-click it and select "Properties" → Select the "Security" tab → Click the "Advanced" button → Go to the "Auditing" tab → Click the "Add" button → Select the following:
- Principal: "Everyone"
- Type: "All"
- Applies to: "This folder, subfolders and files"
- Advanced Permissions: "Delete subfolders and files" and "Delete"
- Run the Group Policy editor (gpedit.msc) and create and edit a new GPO. Specifically, go to → Computer Configuration → Policies → Windows Settings → Security Settings → Local Policies → Audit Policy, and setup as following:
- Audit object access → Define → Success and Failures.
- Go to "Advanced Audit Policy Configuration" → Audit Policies → Object Access, and setup as following:
- Audit File System → Define → Success and Failures
- Audit Handle Manipulation → Define → Success and Failures
- Link the new GPO to your file server.
- Apply your change by forcing a Group Policy update: Go to "Group Policy Management" → Right-click the OU → Click "Group Policy Update".
Reviewing events
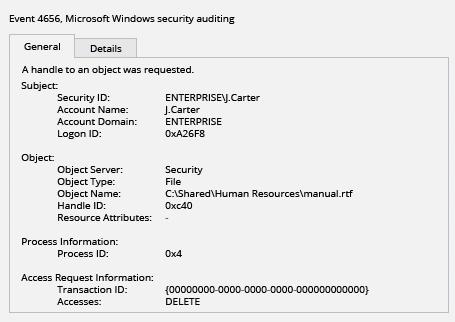
- Open the Event Viewer and search the security log for event ID 4656 with a task category of "File System" or "Removable Storage" and the string "Accesses: DELETE".
- Review the report. The "Subject: Security ID" field will show who deleted each file.
Learn more about Netwrix Auditor for Windows File Servers
Regularly Audit File Deletion to Prevent Business Disruptions
If a file on a server in your domain is deleted, either maliciously or by mistake, users may be unable access critical information they need, causing important business processes to come to a halt. Moreover, without proper file deletion auditing and access permission change auditing, it’s impossible to hold users accountable for their actions and prevent further unauthorized deletions.
Microsoft provides a native method to audit file deletions on Windows file servers. However, you must have already enabled auditing, and the process of searching through Windows event log for deleted files can be quite cumbersome: You’ll have to open each event in the list to find the details, such as the name of the person who deleted the file and the time of the event.
Netwrix Auditor enables you to easily detect and investigate malicious or erroneous file deletions on your Windows file servers, EMC storage devices and NetApp filers. In just a few simple steps, you can get a clear report that shows all changes and access events, including easy-to-read who/what/where/when details. You can even get the reports by email automatically on schedule, and get alerts about specific types of actions so you can respond immediately. The interactive search will simplify and streamline the investigation process. Netwrix Auditor also offers advanced user behavior monitoring that keeps you informed about anomalous activity, such as a surge in access events or mass data deletions, so you can take action before you suffer a breach, data loss or downtime.
Share on
