Sometimes users are granted access rights that enable them to read files containing sensitive data they shouldn’t see. For example, an office manager might mistakenly have permissions to read documents of the Accounting department, which could lead to a security breach. In addition, users sometimes try to read files containing sensitive data they don’t have access to. Making sure to log file access attempts and regularly reviewing those events helps you keep access to sensitive information under control, thereby minimizing the risk of data exfiltration.
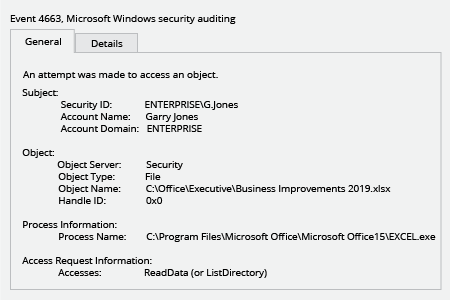
In order to track object access events, you need to enable specific Group Policy settings in Active Directory or local security policy settings on your Windows file server; also, don’t forget to apply NTFS access auditing settings to check that file auditing is properly recorded in the security event log. But once you enable native file access logging, be ready to be swamped by the enormous number of read events generated by your users. To hone in on the events that matter, you need to either configure native filtering settings, which are not very informative and advanced filtering requires deep XML query understanding, or use a third-party solution.
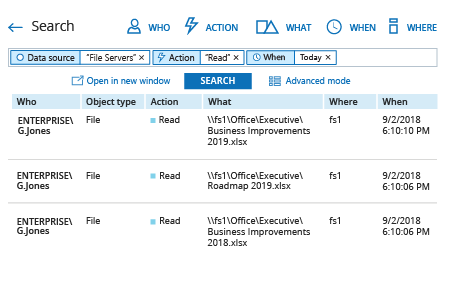
Netwrix Auditor for Windows File Servers is a proven solution that delivers complete visibility into what’s happening on your Windows file servers, including both successful and failed read attempts. The subscription option enables IT pros to get file access auditing reports via email or on their file shares automatically, so they can keep easily an eye on suspicious reads and access attempts, as well as get detailed information about all changes and modified files. With the Interactive Search feature, they can easily investigate any particular file access log. These capabilities help IT administrators stay in control of sensitive data, thwart information security attacks and ensure compliance with regulatory standards.