How to Audit Group Policy Changes using the Security Event Log
Netwrix Auditor for Active Directory
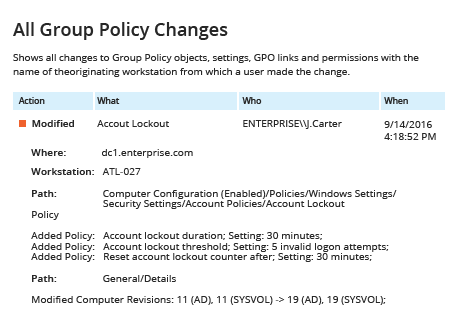
- Run Netwrix Auditor → Navigate to “Reports” → Expand the “Active Directory” section → Go to “Group Policy Changes” → Select “All Group Policy Changes” → Click “View”.
- If you want to get this report by email regularly, simply choose the "Subscribe" option and define the schedule and recipients.
Learn more about Netwrix Auditor for Active Directory
Native Auditing
- To audit changes to Group Policy, you have to first enable auditing: Run gpedit.msc under the administrator account → Create a new Group Policy object (GPO) → Edit it → Go to "Computer Configuration" | Policies | Windows Settings | Security Settings | Advanced Audit Policy Configuration| Audit Policies/DS Access → Click “Audit Directory Service Changes”→ Click “Define” → Choose “Success”.
- Link the new GPO to an OU: Go to "Group Policy Management" → Right-click the OU → Choose "Link an Existing GPO" → Choose the GPO you created.
- Apply your change by forcing a Group Policy update: Go to "Group Policy Management" → Right-click the OU → Click "Group Policy Update".
- Open ADSI Edit → Connect to the Default naming context → Navigate to CN=Policies,CN=System,DC=domain → Open the “Properties of Policies” object → Go to the Security tab → Click the Advanced button → Go to the Auditing tab → Add the Principal "Everyone" → Choose the Type "Success" → For Applies to, click "This object and Descendant objects" → Under Permissions, select following checkboxes: “Create groupPolicyContainer objects”, “Delete”, “Modify Permissions” and “Write versionNumber” → Click "OK".
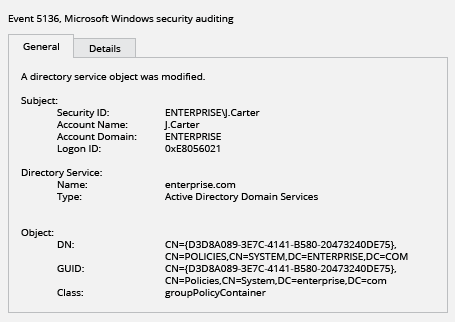
- To review Group Policy changes, open the Event Viewer and search the Security log for event ID 5136 (the Directory Service Changes category).
Audit GPO Changes to Track Aberrant Activity
Group Policy-related events are recorded in the security log on the Microsoft Windows Server domain controller. By reviewing these logs, IT administrators can audit changes to Group Policy. However, although native auditing tools show when and where each change happened, they don’t provide critical details, such as the name of the Group Policy that was changed and the type of action that was performed. To ensure that no aberrant activity slips past your radar, you need additional software that provides more insight into changes to your Group Policy settings.
Netwrix Auditor for Active Directory delivers complete visibility into what’s going on in your Active Directory, including detailed audit reports about changes to Group Policy. The application provides not only the basic information available using native auditing tools, but also critical details such as the name of the Group Policy that was changed, the type of change performed, which user made the change, and the before and after values. Having this information enables IT admins to fully understand Group Policy modifications so they can mitigate the risk of misuse of sensitive data and ensure compliance.
Share on
