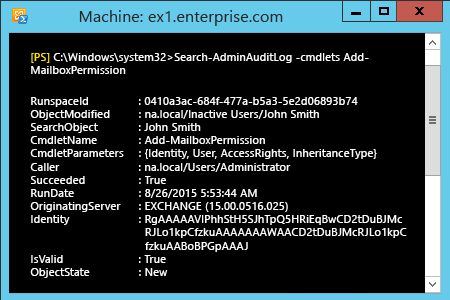
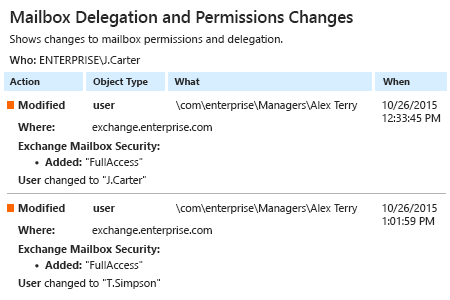
Anyone who has been granted full access permissions to another user’s mailbox can delete or forward emails, change mailbox content and more. These actions can easily go unnoticed by either the mailbox owner or IT staff. Without ongoing tracking of changes in Exchange, full access permissions granted to another user’s mailbox without proper business justification can lead to a security breach. Proper auditing enables IT admins to determine who was granted full access rights to another user’s mailbox, helping them protect critical mailbox content and prevent the loss or leakage of sensitive data.
Netwrix Auditor for Exchange delivers complete visibility into your Microsoft Exchange Server by monitoring all mailbox changes and access events, including mailbox delegation and the granting of full access permissions. With predefined reports on the activity on Exchange Server at hand, IT admins can properly manage full access permissions to mailboxes and quickly determine who was granted full access rights to another user’s mailbox, when it happened and who did it — mitigating the risk of data leaks.