How to Detect Who Deleted a Computer Account in Active Directory
Native Auditing vs. Netwrix Auditor for Active Directory
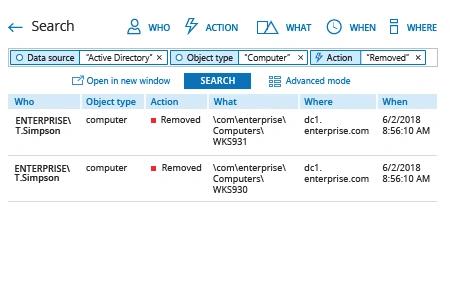
Netwrix Auditor for Active Directory
- Run Netwrix Auditor → Navigate to "Search" → Click on "Advanced mode" if not selected → Set up the following filters:
- Filter = "Data source"
Operator = "Equals"
Value = "Active Directory" - Filter = "Object type"
Operator = "Equals"
Value = "Computer" - Filter = "Action"
Operator = "Equals"
Value = "Removed"
- Filter = "Data source"
- Click the "Search" button and review who deleted computer accounts.
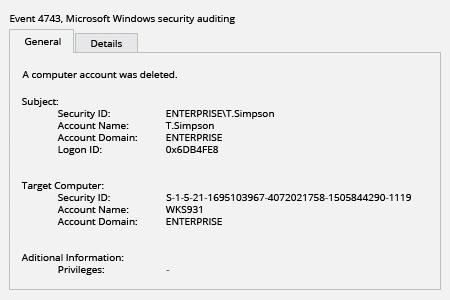
Native Auditing
- Run gpmc.msc → edit "Default Domain Policy" → Computer Configuration → Policies → Windows Settings → Security Settings:
- Local Policies → Audit Policy → Audit account management → Define → Success
- Event Log → Define → Maximum security log size to 1gb and Retention method for security log to Overwrite events as needed.
- Open ADSI Edit → Connect to Default naming context → right click "DC=domain name" → Properties → Security (Tab) → Advanced → Auditing (Tab) → Click "Add" → Choose the following settings:
- Principal: Everyone; Type: Success; Applies to: This object and all descendant objects; Permissions: Delete, Delete subtree, Write all properties → Click "OK".
- To define what computer account was deleted filter Security Event Log for Event ID 4743.
Learn more about Netwrix Auditor for Active Directory
Identify Who Deleted Computer Accounts to Avoid Authentication Errors
Improper deletion of a user account can cause serious problems for an organization. Users whose computer accounts have been deleted won’t be able to log into IT systems using their domain authentication. If they are already logged in, they will have trouble accessing their email, shared folders, SharePoint and other resources. In addition to this loss of productivity, IT staff have to spend time investigating why an authentication error has occurred. To avoid these issues, it’s vitally important to detect the deletion of computer accounts in a timely manner.
Netwrix Auditor for Active Directory enables complete visibility into activity in Active Directory and Group Policy by providing actionable audit data about access events and changes. Customizable email alerts notify IT administrators when anyone deletes computer accounts, so they can respond quickly to unwanted deletions and prevent the problems that arise when the system could not authenticate a user. Audit reports contain actionable details, such as who deleted which computer account and when and where the change occurred, so admins can investigate and prevent similar problems from happening in the future.
Share on
