Netwrix Auditor: Lo strumento di auditing per Microsoft Entra ID
Ferma gli attacchi basati sull'identità. Proteggi Microsoft Entra ID con un monitoraggio panoramico delle modifiche, tracciamento degli accessi e rilevamento delle minacce.
Scopri come li abbiamo aiutati
Affidabile da
































Monitoraggio completo di Entra ID che offre una vista unificata
Sblocca la visibilità ibrida unificata
Utilizza il nostro strumento di auditing Microsoft Entra ID insieme all'Active Directory on-premises per una singola piattaforma in grado di rilevare minacce che attraversano i confini del cloud.
Aumenta la produttività del team IT
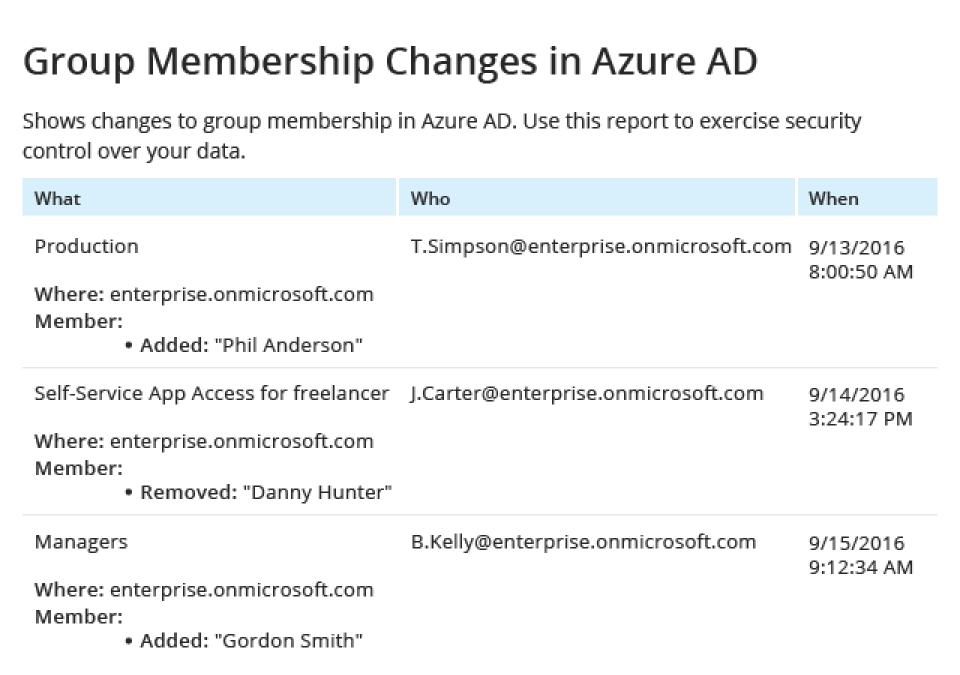
Scoprite rapidamente le cause principali dei problemi che influenzano la vostra Data Security Posture Management e la continuità aziendale. Automatizzate i compiti di controllo dei cambiamenti e di reporting.
Individua account compromessi
Ottieni visibilità sui cambiamenti di sicurezza e configurazione, come l'escalation dei privilegi, attività amministrative anomale e altro ancora.
Superare le verifiche con meno sforzo
Rapporti preimpostati per la conformità PCI DSS, HIPAA, GDPR e SOX e una ricerca interattiva per rispondere rapidamente alle domande degli ispettori.
Capacità
Auditing dell'ID con l'intelligenza necessaria per anticipare le minacce all'identità basate sul cloud
Pronto per iniziare?
Soluzioni
Vai oltre la protezione da una singola minaccia. Assicura ogni angolazione con le soluzioni Netwrix.
Fidato dai professionisti
Non fidarti solo di quello che diciamo
Integrazioni
Integrazioni senza soluzione di continuità per una sicurezza più intelligente
Vedi tutte le integrazioni





