User account lockouts are very common — they can happen whenever a user enters a wrong password more times than permitted by the organization’s security policy. Locked-out users are temporarily left without access to critical business systems like Exchange or SharePoint. In these cases, account lockouts can be dealt with quickly once the locked user reports not being able to access critical services. But lockouts can happen for other reasons as well, and it can require quite a lot of work for IT administrators to learn exactly why the Active Directory user accounts were locked out; they can spend hours on Active Directory PowerShell scripting. Moreover, if they’re asked to regularly review locked out user accounts, they’ll need to periodically run PowerShell commands to get locked out users. But there’s a better way.
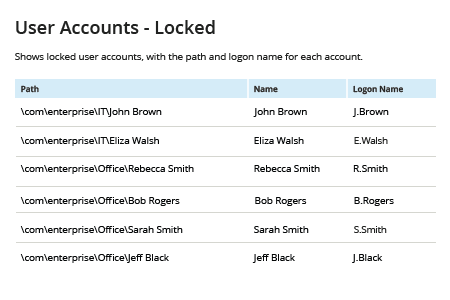
Netwrix Auditor for Active Directory simplifies the job by providing a ready-to-use report that lists all locked out users, along with the path and logon name for each account, so you can promptly check locked accounts and either restore access or disable or delete the account to maintain good IT hygiene. Plus, its Account Lockout Examiner tool can alert you in real time whenever an account is locked so you can quickly restore access for legitimate users, minimizing user frustration, productivity losses and helpdesk workload.