Netwrix Auditor for Windows Server
- Run Netwrix Auditor → Navigate to Reports → Open “Windows Server” → Go to “Windows Server - State-in-Time” → Select “File Shares on Windows Servers” → Click “View”.
- To save the report, click the “Export” button and choose PDF, Word or Excel format. To receive the report regularly by email, click the “Subscribe” button and choose the schedule you prefer.
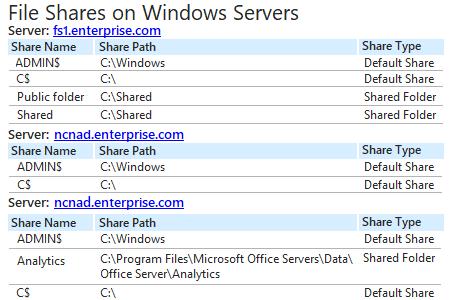
Sample report:
Learn more about Netwrix Auditor for Windows Server
Native Auditing
- Open the Powershell ISE → Create new script with the following code and run it, specifying the path for the export:
# Import the AD module to the session
Import-Module ActiveDirectory
# Retrieve the dNSHostName attribute from all computer accounts in AD
$ComputerNames = Get-ADComputer -Filter * -Properties dNSHostName |Select-Object -ExpandProperty dNSHostName
$AllComputerShares = @()
foreach($Computer in $ComputerNames)
{
try{
$Shares = Get-WmiObject -ComputerName $Computer -Class Win32_Share -ErrorAction Stop
$AllComputerShares += $Shares
}
catch{
Write-Error "Failed to connect retrieve Shares from $Computer"
}
}
# Select the computername and the name, path and comment of the share and Export
$AllComputerShares |Select-Object -Property PSComputerName,Name,Path,Description |Export-Csv -Path C:\data\pcshares.csv -NoTypeInformation
- Open the file produced by the script in MS Excel.
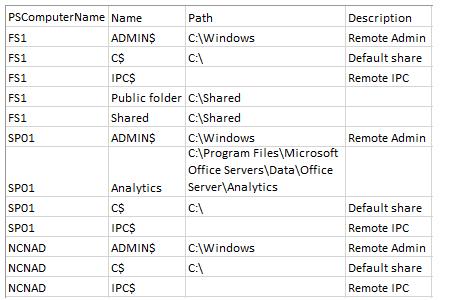
Sample report:
Regularly View Shared Folders Reports to Spot Deviations from a Known Good Baseline
By default, the Microsoft Windows operating system creates a number of hidden shared folders, called “admin shares,” that are accessible only to users with administrative privileges. In addition, users can create non-default shared folders using Windows Explorer in order to share information across the network. Since both types of shared folders can contain sensitive information, to maintain data security and minimize the risk of data breaches, you need to review a list of shared folders across your Windows servers on a regular basis, so you can exercise proper security control over your files and folders.
Netwrix Auditor for Windows Server enables you to check shared folders across all of your servers and quickly spot any suspicious shares that deviate from your known good baseline, in accordance with computer management best practices. The list of file shares includes the name and type of every file share on a specific Windows server, so you can reduce your attack surface area with regular cleanup.
Share on
