Back
Netwrix Auditor: The SQL Server Monitoring Tool
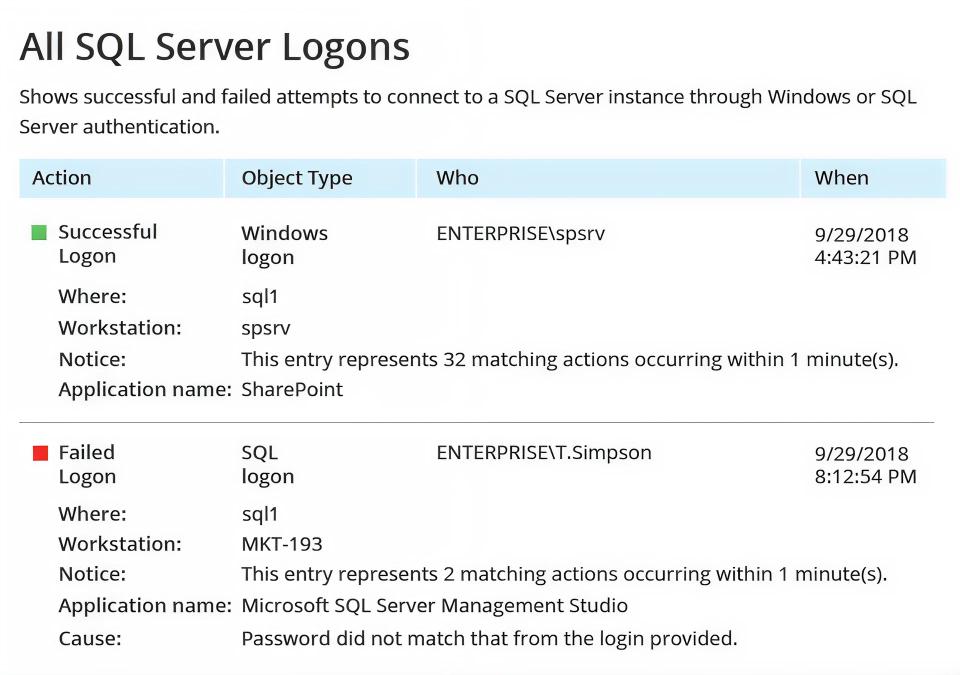
Audit every logon, permission elevation, and schema change with an advanced, in-depth SQL Server monitoring tool.
Read their Stories
Trusted by
































Why Netwrix?
Straightforward SQL Server audit software that boosts security and productivity
Minimize the risk of a data breach
Harden the security of structured data with SQL Server monitoring tools by exposing loose permissions and spotting critical actions.
Pass compliance audits with less effort
Generate ready-to-present reports for PCI DSS, HIPAA, GDPR, SOX, GLBA, FISMA, CJIS, and other regulatory frameworks.
Increase the productivity of DBAs
Spot, investigate, and remediate unwanted changes, such as the accidental deletion of a database table.
Instance-wide audit coverage
Monitor configuration changes, database modifications, and user activities across every SQL Server instance in your environment.
Capabilities
SQL Server monitoring that answers compliance questions fast, when you need SQL audit data most
See for yourself
Ready to get started?
Solutions
Go beyond single-threat protection. Secure every angle with Netwrix solutions.
Trusted by professionals
Don’t just take our word for it








