Netwrix Auditor: The SharePoint Audit Tool
Track every document change, permission tweak, and file activity with a comprehensive SharePoint and Teams monitoring tool.
Read their Stories
Trusted by
































Identify and mitigate risks with Teams and SharePoint monitoring
Spot and fix data security issues
Identify and mitigate risks around sensitive data before they turn into a breach by getting deep visibility into data sensitivity and spotting overexposed content.
Pass compliance audits with less effort
Streamline compliance using out-of-the-box reports aligned with GDPR, PCI DSS, FISMA/NIST, HIPAA, and many other regulations.
Increase the productivity of IT teams
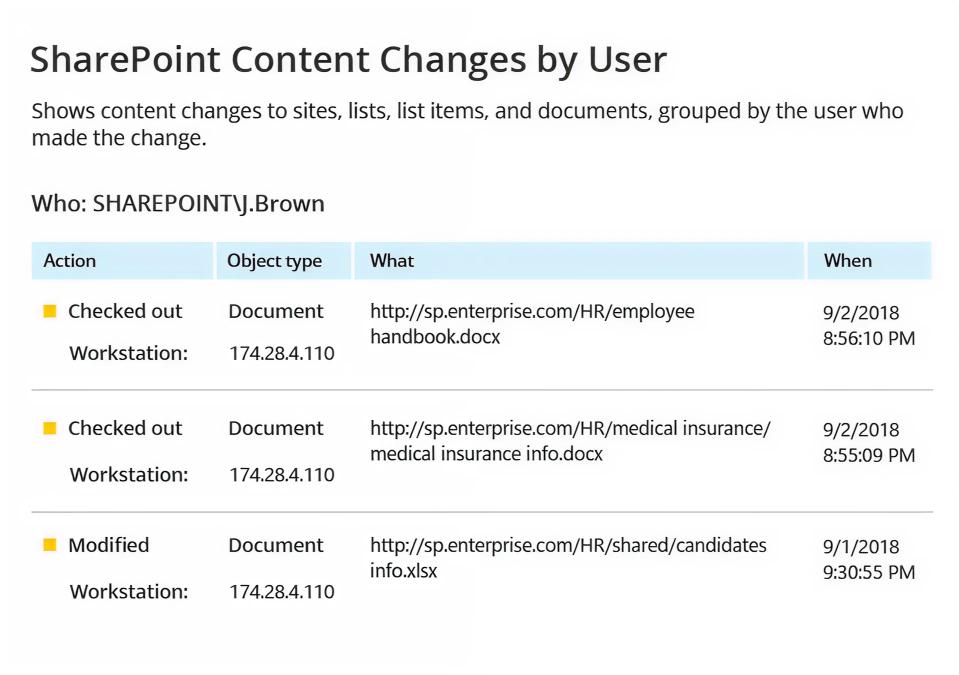
Uncover, investigate, and remediate critical changes in our SharePoint Audit Tool — no need to dig through cryptic native logs or manually correlate events.
Delegate access reviews
Enable data owners to approve access requests and conduct reviews, reducing IT workload while improving accuracy.
Capabilities
Protect your most sensitive data without risking productivity or creating unnecessary bottlenecks
Ready to get started?
Solutions
Go beyond single-threat protection. Secure every angle with Netwrix solutions.
Trusted by professionals
Don’t just take our word for it








