Detect security threats, prove compliance and increase IT team efficiency with IT audit software from Netwrix
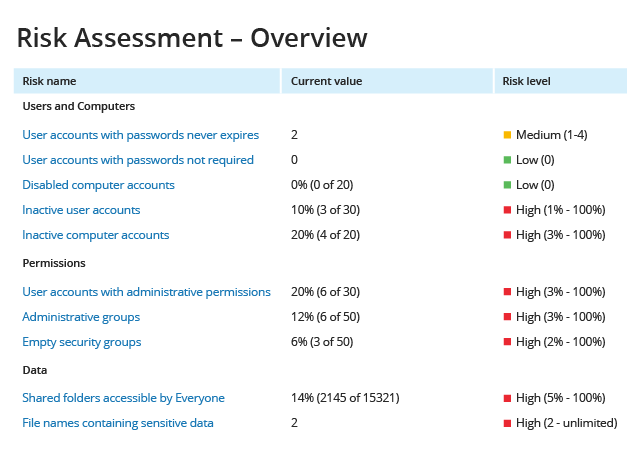
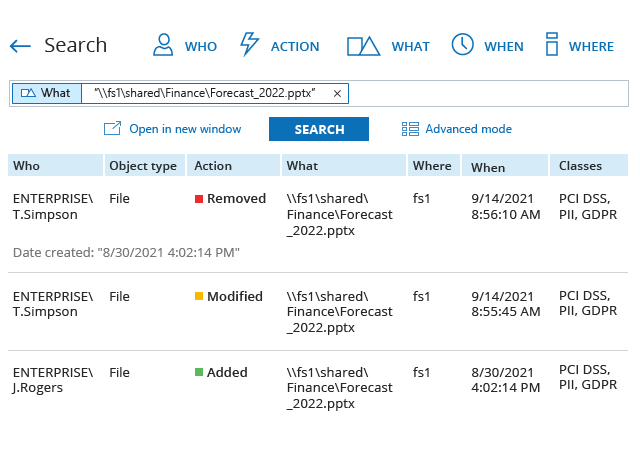
More and more organizations, regardless of size or industry, are recognizing the value of conducting regular internal and external IT audits. The benefits are many: IT auditing can help you improve security, pass compliance audits and optimize IT operations. But all too often, the process is far more cumbersome and time-consuming than it needs to be. Learn how Netwrix Auditor software can help you improve your security posture, ease the auditing burden and achieve your goals with far less effort.
Audit your most important IT systems from a centralized platform
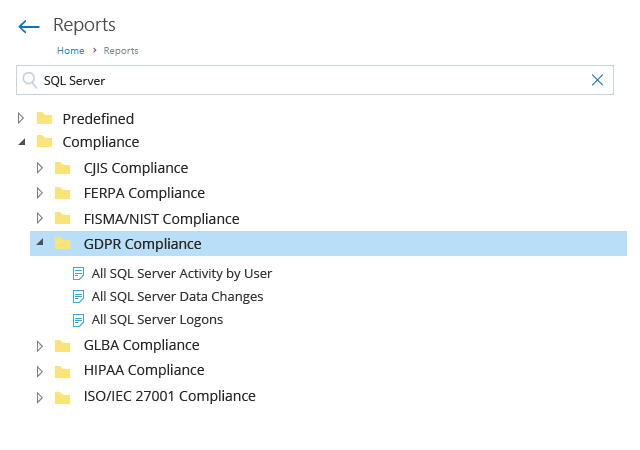
Are you tired of juggling multiple auditing and reporting tools in an attempt to collect audit information from all your on-premises and cloud-based systems? Do you need a software solution that delivers that information in a unified and consistent way? Netwrix Auditor provides a consolidated audit trail across a wide variety of IT systems, including Active Directory, Windows Server, Oracle Database and network devices.