- Run GPMC.msc (url2open.com/gpmc) → Create a new GPO and edit it → Computer Configuration → Policies → Windows Settings → Security Settings → Local Policies → Audit Policy:
- Audit account management → Define → Success
- Audit directory service access → Define → Success.
- Return to the Security Settings level → Event Log:
- Maximum security log size → Define to 4gb
- Retention method for security log → Define to Overwrite events as needed.
- Link the new GPO: Go to "Group Policy Management" → Right-click domain or OU → Choose Link an Existing GPO → Choose the GPO that you created.
- Force the group policy update: In "Group Policy Management" right-click on the defined OU → Click "Group Policy Update".
- Open ADSI Edit (url2open.com/adsi) → Right-click ADSI Edit → Connect to Default naming context → Right-click DomainDNS object with the name of your domain → Properties → Security (Tab) → Advanced (Button) → Auditing (Tab) → Add Principal "Everyone" → Type "Success" → Applies to "This object and Descendant objects" → Permissions → Select all check boxes by clicking on "Full Control", except the following: Full Control, List Contents, Read all properties, Read permissions → Click "OK".
- Open Event viewer and filter Security log to find event id's (Windows Server 2003/2008-2012):
- 4727, 4731, 4754, 4759, 4744, 4749 – Group created
- 4728, 4732, 4756, 4761, 4746, 4751 – Member added to a group
- 4729, 4733, 4757, 4762, 4747, 4752 – Member removed from a group
- 4730, 4734, 4758, 4748, 4753, 4763 – Group deleted
- 4735, 4737, 4745, 4750, 4755, 4760 – Group changed
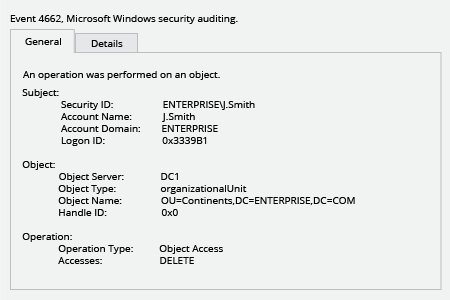
- 4662 - An operation was performed on an object (Type: Directory Service Access).
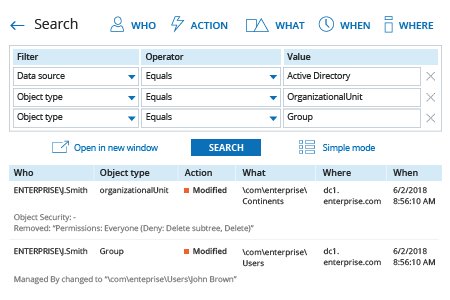
- Run Netwrix Auditor → Navigate to "Search" → Click on "Advanced mode" if not selected → Set up the following filters:
- Filter = "Data source"
Operator = "Equals"
Value = "Active Directory" - Filter = "Object type"
Operator = "Equals"
Value = "OrganizationalUnit" - Filter = "Object type"
Operator = "Equals"
Value = "Group"
- Filter = "Data source"
- Click the "Search" button and review what changes were made to groups and organizational units.
In order to create an alert on organizational units and groups modifications:
- From the search results, navigate to "Tools" → Click "Create alert" → Specify the new alert’s name.
- Switch to the "Recipients" tab → Click "Add Recipient" → Specify the email address where you want the alert to be delivered.
- Click "Add" to save the alert.