How to Detect Who Deleted a User Account in Active Directory
Native Solution vs. Netwrix Auditor for Active Directory
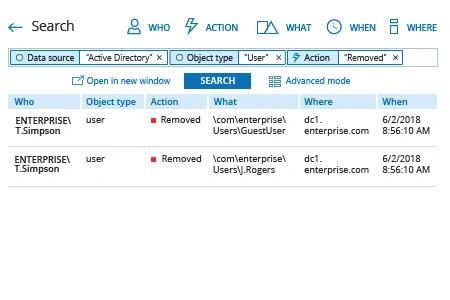
Netwrix Auditor for Active Directory
- Run Netwrix Auditor → Navigate to "Search" → Click on "Advanced mode" if not selected → Set up the following filters:
- Filter = "Data source"
Operator = "Equals"
Value = "Active Directory" - Filter = "Object type"
Operator = "Equals"
Value = "User" - Filter = "Action"
Operator = "Equals"
Value = "Removed"
- Filter = "Data source"
- Click the "Search" button and review who deleted user accounts.
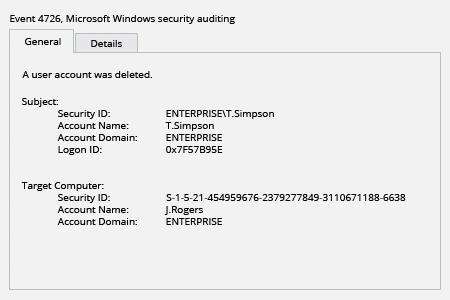
Native Auditing
- Run GPMC.msc → open “Default Domain Policy” → Computer Configuration → Policies → Windows Settings → Security Settings:
- Local Policies → Audit Policy → Audit account management → Define → Success
- Event Log → Define → Maximum security log size to 1gb and Retention method for security log to Overwrite events as needed.
- Open ADSI Edit → Connect to Default naming context → right click “DC=domain name” → Properties → Security (Tab) → Advanced → Auditing (Tab) → Click “Add” → Choose the following settings:
- Principal: Everyone
- Type: Success
- Applies to: This object and all descendant objects
- Permissions: Delete all child objects → Click “OK”.
- In order to define what user account was deleted and who deleted it filter Security Event Log for Event ID 4726.
Learn more about Netwrix Auditor for Active Directory
Detect and Investigate User Account Deletions to Avoid System Unavailability
When somebody deletes user accounts, these users will not be able to log into IT systems using domain authentication from any computer within the organization. If you delete a user account while the user is logged in, the user will lose access to email, SharePoint, SQL Server, shared folders and other systems. Therefore, it’s essential to monitor account deletions and quickly determine who deleted a user account, so you can quickly restore any improperly deleted account to minimize the risk of business disruption and system unavailability.
Netwrix Auditor for Active Directory delivers security analytics about what’s going on in Active Directory and Group Policy. It enables you to track all activity in Active Directory, including when anyone deleted a user account. It also automates reporting tasks by letting IT pros subscribe to predefined reports that are delivered via email, keeping them aware of who deleted any account, and where and when it was done. They can also generate custom reports using Interactive Search to detect and investigate suspicious activity, and save their search criteria for later use.
Share on
