See all products
Netwrix Data Classification Software
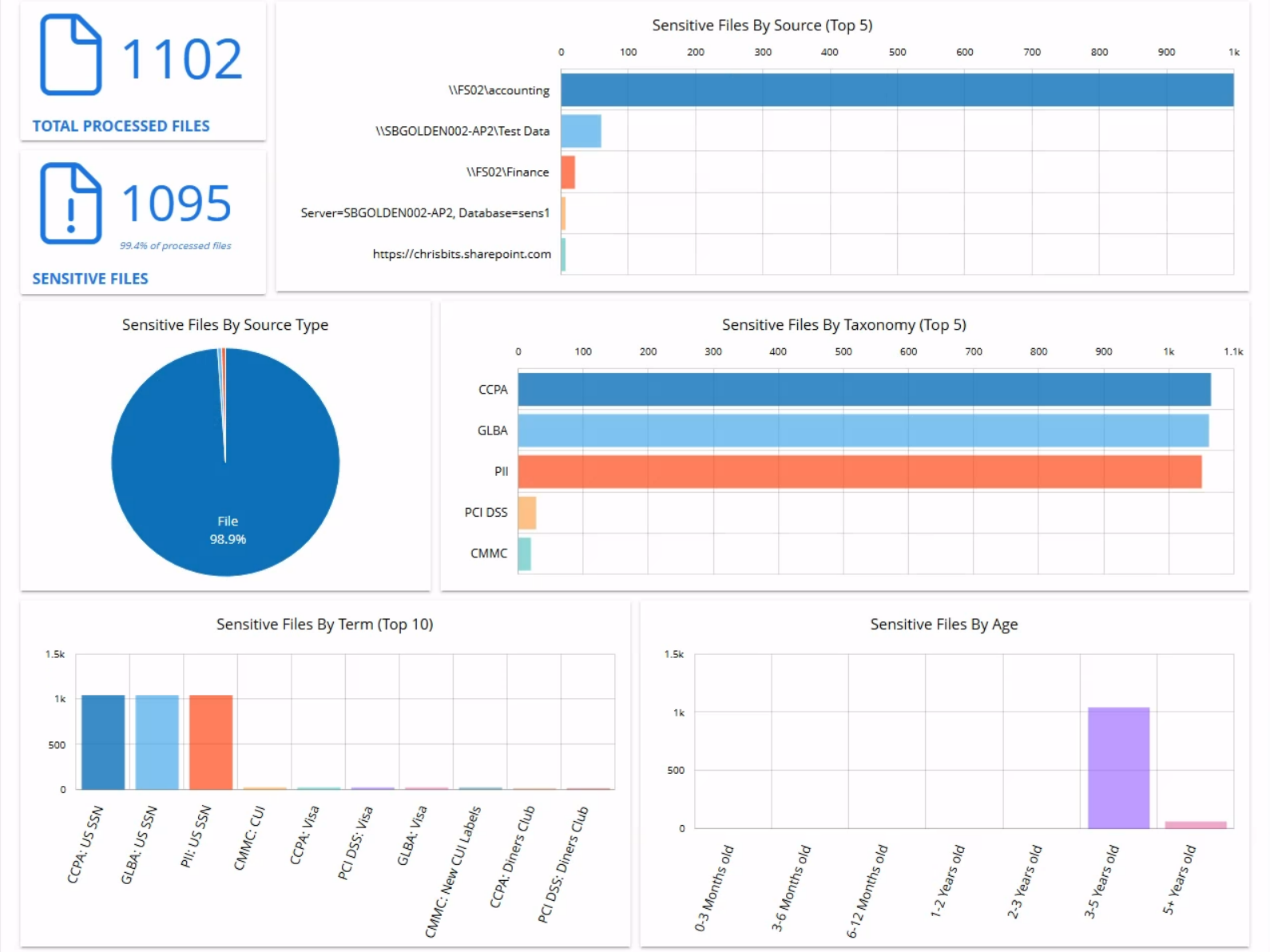
Discover, classify, and secure sensitive data across your environments with intelligent data classification solutions.
Read their Stories
Trusted by
































Why Netwrix?
Data classification tools that focus on what matters
Find sensitive data everywhere
Automatically unearth sensitive data across on-prem and cloud environments and remediate overexposure with automated workflows.
Clean up ROT data
Shore up attack avenues by identifying and removing redundant, obsolete, and trivial data that creates potential exposure.
Automate compliance discovery
Easily achieve GDPR, HIPAA, PCI DSS, and other compliance with automated discovery and predefined classification rules for regulated data.
Safeguard intellectual property
Quickly identify and secure your intellectual property with advanced machine learning, without the high cost of professional services.
Capabilities
Data classification software that detects, classifies, and manages sensitive data with less effort across your entire IT infrastructure
See for yourself
Ready to get started?
Solutions
Go beyond single-threat protection. Secure every angle with Netwrix solutions.
Trusted by professionals
Don’t just take our word for it







